CWE Compatibility for Red Hat Customer Portal
What is CWE?
Common Weakness Enumeration (CWE) is a dictionary or formal list of common software weaknesses. It is a common language or taxonomy for describing vulnerabilities and weaknesses; a standard measurement for software assurance tools and services' capabilities; and a base for software vulnerability and weakness identification, mitigation, and prevention.
What is CWE Compatibility?
The CWE Compatibility and Effectiveness Program is a formal review and evaluation process for declaring products and services as CWE-Compatible and CWE-Effective. Red Hat is engaged in CWE Compatibility and Effectiveness Program and is working towards fulfilling its requirements for providing a common language for discussing, identifying, and dealing with the causes of vulnerabilities in its products as part of its assessment services, knowledge repositories, software development practices, and education offerings.
How is CWE used?
For understanding how CWE identifiers are assigned to Red Hat vulnerabilities, you also need to understand some elements of CWE terminology. CWE identifiers—also known as CWE IDs or CWEs—are organized into four main types: (a) Category, (b) Compound Element, (c) View, and (d) Weakness.
- Category IDs are assigned to sets of weaknesses sharing one or more common attributes.
- Compound Element IDs are assigned to combinations of weaknesses (i.e. Composites and Named Chains—more on these later.)
- View IDs are assigned to predefined perspectives with which you might look at weaknesses.
- Weakness IDs are assigned to the actual software weaknesses themselves.
Weaknesses are also organized into three main types: (a) Class, (b) Base, and (c) Variant.
- Class is the most abstract type of weakness.
- Base is a more specific type of weakness that is still mostly independent of a specific resource or technology.
- Variant is a weakness specific to a particular resource, technology, or context.
Due to the diverse nature of our products, the preferred type of weakness for CWE assignments are weakness bases. Weakness classes are used in cases that there are research gaps, and it turns out to be difficult to make consistent CWE assignments using related weakness bases.
Weaknesses IDs are assigned to Red Hat vulnerabilities in chains. A chain is a sequence of two or more weaknesses closely linked together. Where one weakness X, can directly create the conditions necessary to cause another weakness Y, resulting in a vulnerability. In such cases, CWE refers to X as primary to Y, and Y as resultant from X.
A named chain is a noted commonly recurring chain that has received its own CWE identifier. A composite is an inclusive combination of two or more weaknesses or chains that forms another named weakness or vulnerability. For additional information, refer to the CWE Glossary.
Differently from what security assessment tools do—with a few exceptions, such as integer overflows and variants—vulnerabilities are commonly named and reported as its resultant weaknesses, with little or no additional research from the reporting party. Thus, it is up to Red Hat to reverse the chain to properly identify the cause of the vulnerability.
You may use the Bugzilla search interface to find vulnerabilities corresponding to one or more CWE identifiers.
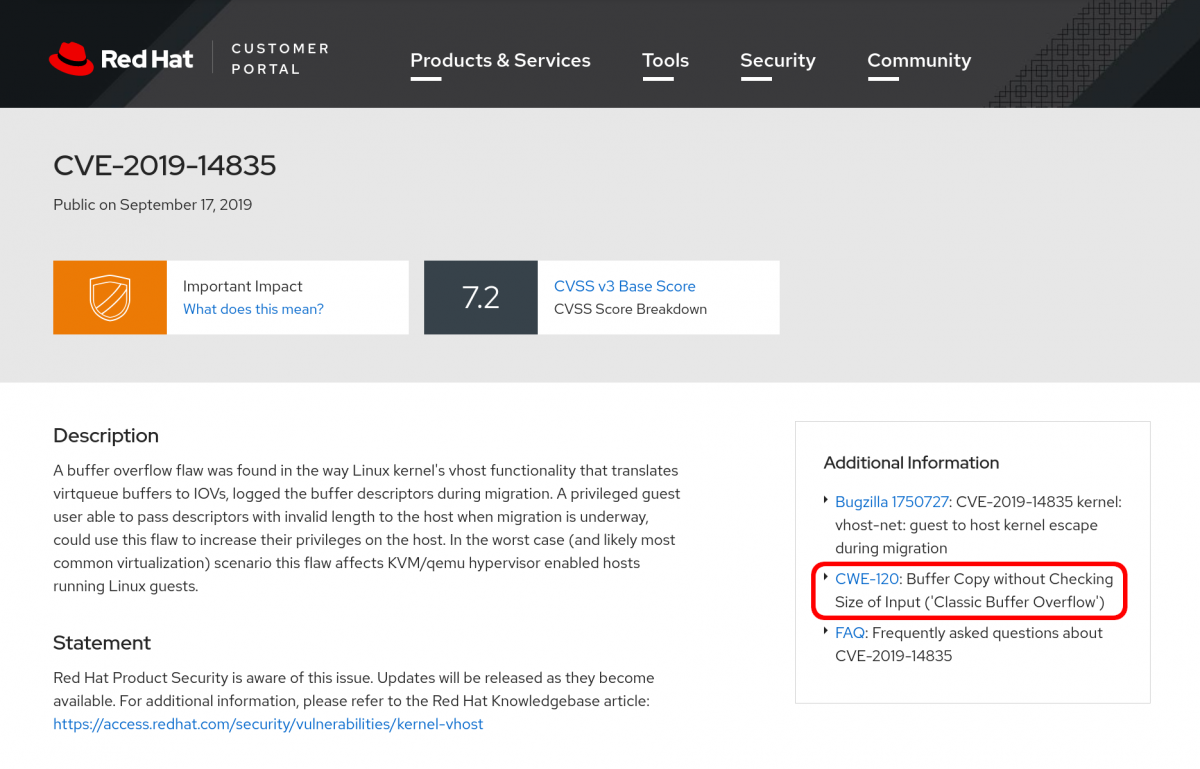
In individual CVE pages, each CWE element listed is linked to the page containing its detailed description at the MITRE web site.
The CWE coverage for Red Hat Customer Portal is reviewed and updated twice a year, along with the release of a vulnerability assessment report. CWE identifiers are assigned to Red Hat vulnerabilities using the present CWE coverage at the time of the vulnerability assessment. Thus, references to vulnerabilities are divided into time slices based upon the date the vulnerability was assessed and the present CWE coverage at that time. For additional information, refer to the CWE Coverage for Red Hat Customer Portal.


Comments