14.2.4. Using Key-Based Authentication
To improve the system security even further, you can enforce key-based authentication by disabling the standard password authentication. To do so, open the
/etc/ssh/sshd_config configuration file in a text editor such as vi or nano, and change the PasswordAuthentication option as follows:
PasswordAuthentication no
To be able to use
ssh, scp, or sftp to connect to the server from a client machine, generate an authorization key pair by following the steps below. Note that keys must be generated for each user separately.
Red Hat Enterprise Linux 6 uses SSH Protocol 2 and RSA keys by default (see Section 14.1.3, “Protocol Versions” for more information).
Important
Do not generate key pairs as
root, as only root would be able to use those keys.
Note
Before reinstalling your system, back up the
~/.ssh/ directory to keep the generated key pair. Copy the backed-up data to the home directory in the new system for any user you require, including root.
14.2.4.1. Generating Key Pairs
To generate an RSA key pair for version 2 of the SSH protocol, follow these steps:
- Generate an RSA key pair by typing the following at a shell prompt:
~]$
ssh-keygen -t rsaGenerating public/private rsa key pair. Enter file in which to save the key (/home/john/.ssh/id_rsa): - Press Enter to confirm the default location (that is,
~/.ssh/id_rsa) for the newly created key. - Enter a passphrase, and confirm it by entering it again when prompted to do so. For security reasons, avoid using the same password as you use to log in to your account.After this, you will be presented with a message similar to this:
Your identification has been saved in /home/john/.ssh/id_rsa. Your public key has been saved in /home/john/.ssh/id_rsa.pub. The key fingerprint is: e7:97:c7:e2:0e:f9:0e:fc:c4:d7:cb:e5:31:11:92:14 john@penguin.example.com The key's randomart image is: +--[ RSA 2048]----+ | E. | | . . | | o . | | . .| | S . . | | + o o ..| | * * +oo| | O +..=| | o* o.| +-----------------+
- Change the permissions of the
~/.ssh/directory:~]$
chmod 700 ~/.ssh - Copy the content of
~/.ssh/id_rsa.pubinto the~/.ssh/authorized_keyson the machine to which you want to connect, appending it to its end if the file already exists. - Change the permissions of the
~/.ssh/authorized_keysfile using the following command:~]$
chmod 600 ~/.ssh/authorized_keys
To generate a DSA key pair for version 2 of the SSH protocol, follow these steps:
- Generate a DSA key pair by typing the following at a shell prompt:
~]$
ssh-keygen -t dsaGenerating public/private dsa key pair. Enter file in which to save the key (/home/john/.ssh/id_dsa): - Press Enter to confirm the default location (that is,
~/.ssh/id_dsa) for the newly created key. - Enter a passphrase, and confirm it by entering it again when prompted to do so. For security reasons, avoid using the same password as you use to log in to your account.After this, you will be presented with a message similar to this:
Your identification has been saved in /home/john/.ssh/id_dsa. Your public key has been saved in /home/john/.ssh/id_dsa.pub. The key fingerprint is: 81:a1:91:a8:9f:e8:c5:66:0d:54:f5:90:cc:bc:cc:27 john@penguin.example.com The key's randomart image is: +--[ DSA 1024]----+ | .oo*o. | | ...o Bo | | .. . + o. | |. . E o | | o..o S | |. o= . | |. + | | . | | | +-----------------+
- Change the permissions of the
~/.ssh/directory:~]$
chmod 700 ~/.ssh - Copy the content of
~/.ssh/id_dsa.pubinto the~/.ssh/authorized_keyson the machine to which you want to connect, appending it to its end if the file already exists. - Change the permissions of the
~/.ssh/authorized_keysfile using the following command:~]$
chmod 600 ~/.ssh/authorized_keys
To generate an RSA key pair for version 1 of the SSH protocol, follow these steps:
- Generate an RSA key pair by typing the following at a shell prompt:
~]$
ssh-keygen -t rsa1Generating public/private rsa1 key pair. Enter file in which to save the key (/home/john/.ssh/identity): - Press Enter to confirm the default location (that is,
~/.ssh/identity) for the newly created key. - Enter a passphrase, and confirm it by entering it again when prompted to do so. For security reasons, avoid using the same password as you use to log into your account.After this, you will be presented with a message similar to this:
Your identification has been saved in /home/john/.ssh/identity. Your public key has been saved in /home/john/.ssh/identity.pub. The key fingerprint is: cb:f6:d5:cb:6e:5f:2b:28:ac:17:0c:e4:62:e4:6f:59 john@penguin.example.com The key's randomart image is: +--[RSA1 2048]----+ | | | . . | | o o | | + o E | | . o S | | = + . | | . = . o . .| | . = o o..o| | .o o o=o.| +-----------------+
- Change the permissions of the
~/.ssh/directory:~]$
chmod 700 ~/.ssh - Copy the content of
~/.ssh/identity.pubinto the~/.ssh/authorized_keyson the machine to which you want to connect, appending it to its end if the file already exists. - Change the permissions of the
~/.ssh/authorized_keysfile using the following command:~]$
chmod 600 ~/.ssh/authorized_keys
See Section 14.2.4.2, “Configuring ssh-agent” for information on how to set up your system to remember the passphrase.
Important
Never share your private key with anybody; it is for your personal use only.
14.2.4.2. Configuring ssh-agent
To store your passphrase so that you do not have to enter it each time you initiate a connection with a remote machine, you can use the
ssh-agent authentication agent. If you are running GNOME, you can configure it to prompt you for your passphrase whenever you log in and remember it during the whole session. Otherwise you can store the passphrase for a certain shell prompt.
To save your passphrase during your GNOME session, follow these steps:
- Make sure you have the openssh-askpass package installed. If not, see Section 8.2.4, “Installing Packages” for more information on how to install new packages in Red Hat Enterprise Linux.
- Select
from the panel. The Startup Applications Preferences will be started, and the tab containing a list of available startup programs will be shown by default. 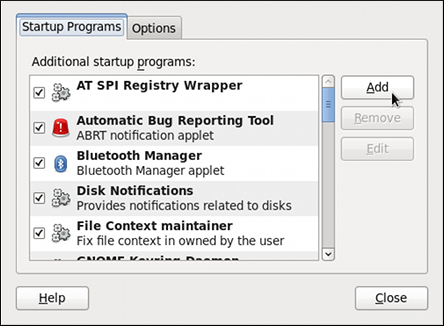
Figure 14.1. Startup Applications Preferences
- Click the button on the right, and enter
/usr/bin/ssh-addin the Command field.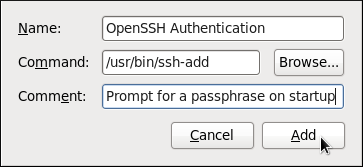
Figure 14.2. Adding new application
- Click and make sure the check box next to the newly added item is selected.
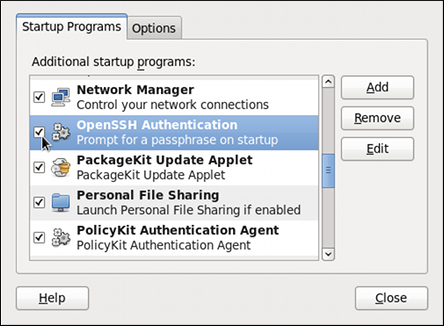
Figure 14.3. Enabling the application
- Log out and then log back in. A dialog box will appear prompting you for your passphrase. From this point on, you should not be prompted for a password by
ssh,scp, orsftp.
Figure 14.4. Entering a passphrase
To save your passphrase for a certain shell prompt, use the following command:
~]$ ssh-add
Enter passphrase for /home/john/.ssh/id_rsa:
Note that when you log out, your passphrase will be forgotten. You must execute the command each time you log in to a virtual console or a terminal window.
14.2.4.3. Multiple required methods of authentication for sshd
For higher security, SSH can require multiple methods of authentication to log in successfully, for example both a passphrase and a public key. Set the
RequiredAuthentications2 option in the /etc/ssh/sshd_config file as desired, for example by running:
~]# echo "RequiredAuthentications2 publickey,password" >> /etc/ssh/sshd_config
For more information on the available options, see the
sshd_config(5) manual page.