-
Language:
English
-
Language:
English
Red Hat Training
A Red Hat training course is available for Red Hat JBoss Operations Network
Initial Setup: the Resource Inventory, Groups, and Users
for initially setting up resources and security in JBoss ON
Abstract
1. Using the JBoss ON Web Interface
1.1. Logging into the JBoss ON Web UI
rhq-server.properties file, JBoss ON is completely administered through its web interface.
http://server.example.com:7080
rhqadmin.
Figure 1. Logging into JBoss ON
Note
1.2. A High Level Walk-Through
- The top menu
- The left menu tables
- The dashboard
- Resource-based tables, which can be for the resource inventory, a summary report, or the results of a search
- Configuration pages which both provide details for and access to elements in JBoss ON, including resources, groups, plug-ins, and JBoss ON server settings
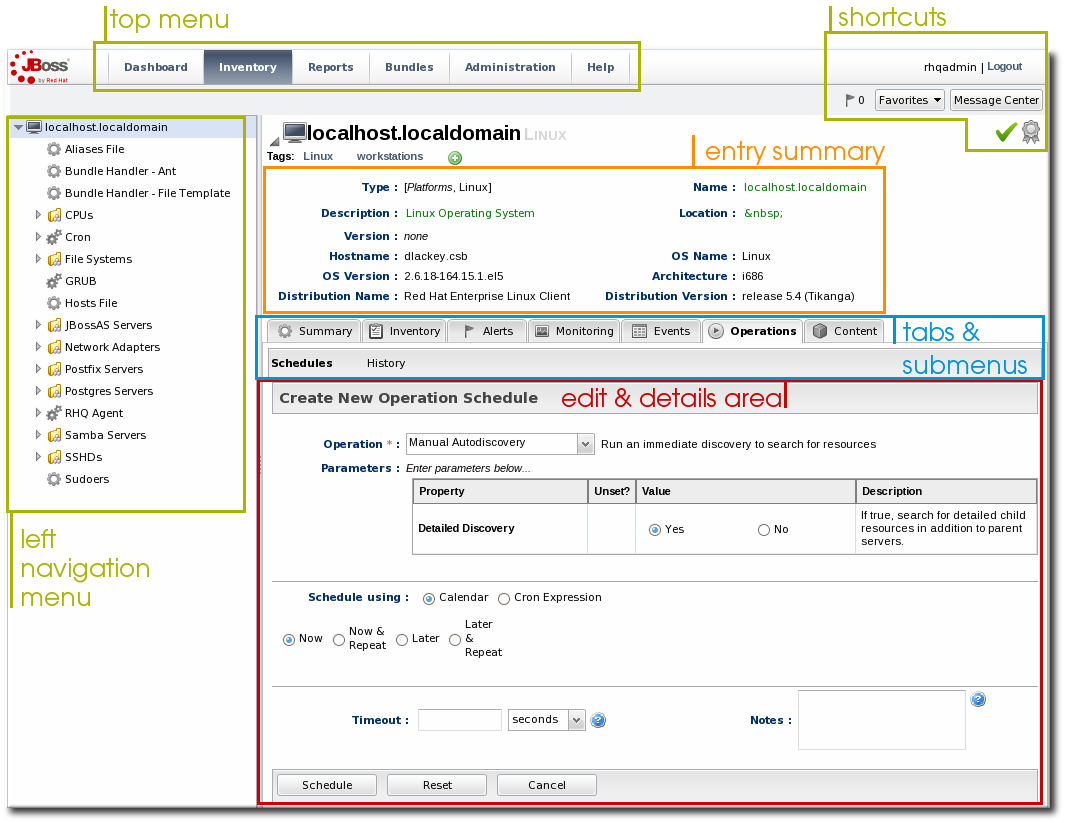
Figure 2. UI Elements All Together
1.2.1. The Top Menu
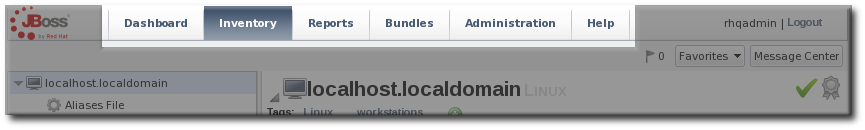
Figure 3. The Top Menu
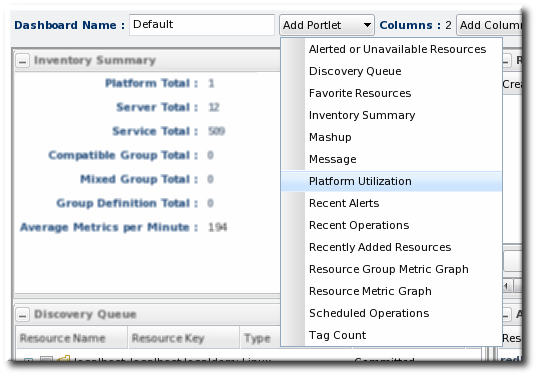
- The Dashboard contains a global overview of JBoss ON and its resources. Different, configurable snapshot summaries (called portlets) show different aspects of the resources and server, such as the discovery queue, recent alerts, recent operations, and resource counts.
- The Inventory tab shows both resources and groups.
- The Reports tab shows pre-defined reports. These are slightly different than the Dashboard, which focuses exclusively on resource information: the reports look at the current actions of the different subsystem (or major functional areas) of JBoss ON, such as alerts, operations, metric collection, and configuration history.
- The Bundles tab opens the provisioning and content functional area. This is for uploading and deploying content bundles that are used to provision new applications.
- Administration goes to all areas related to configuring the JBoss ON server itself. This includes server settings, plug-ins, users and security, and agent settings.
1.2.2. The Left Menu
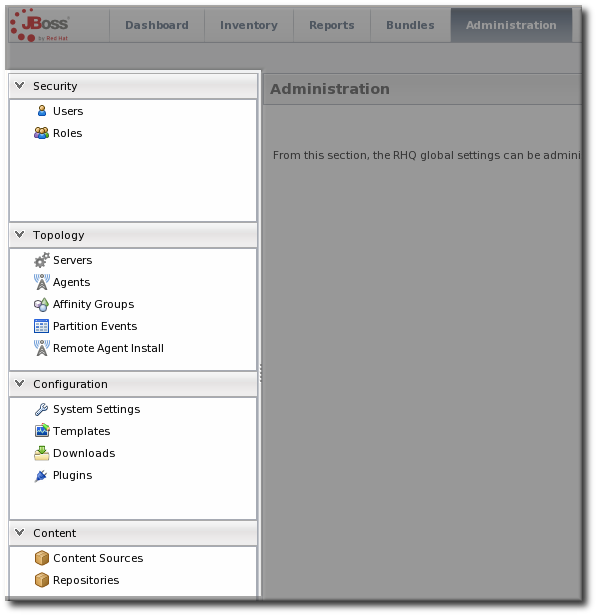
Figure 4. The Left Menu
Figure 5. Collapsing the Left Menu
1.2.3. Dashboard
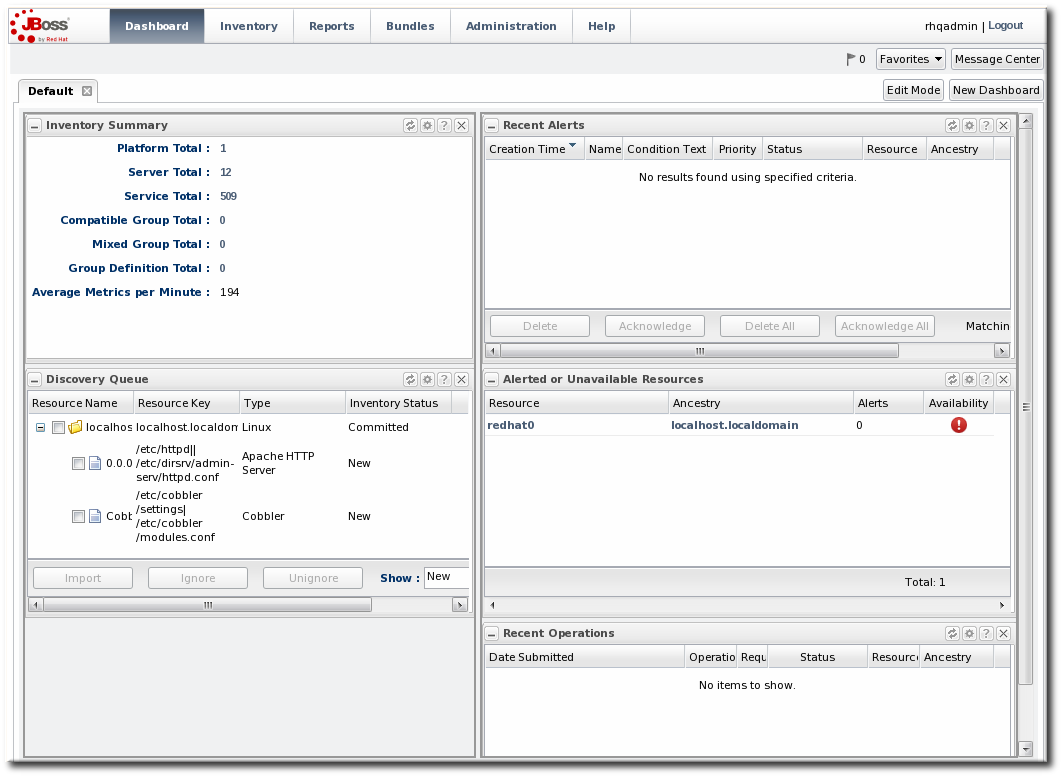
Figure 6. Dashboard View
1.2.4. Inventory Browsers and Summaries
- Tabs for different areas, with subtabs that further break down information
- A table of results
- Icons that open a configuration or task option for that specific entity
- Buttons that perform actions (create, delete, or some other specific action) on the entries; some of these buttons aren't active unless an entry is selected
Figure 7. Inventory Browser
1.2.5. Entry Details Pages
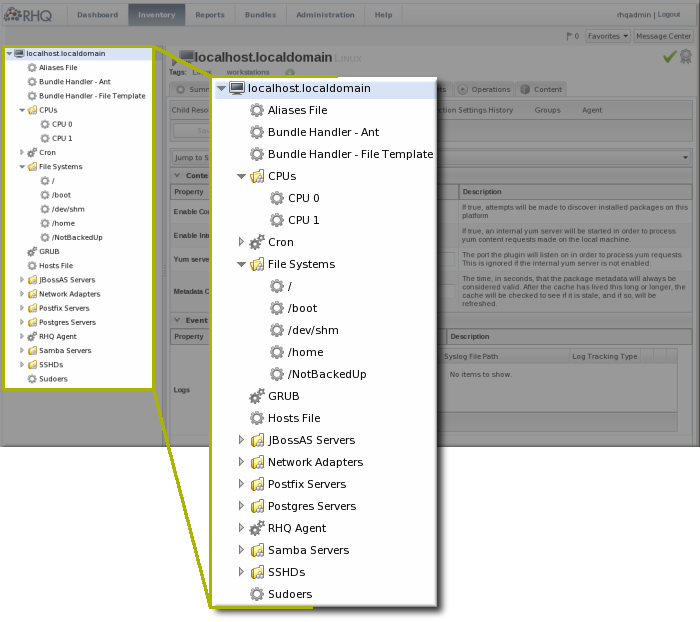
Figure 8. Resource Tree
Note
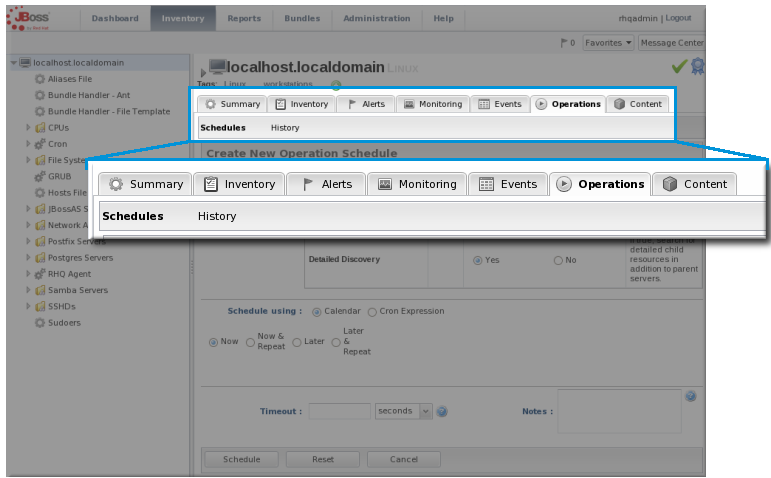
Figure 9. Tabs for a Resource Entry
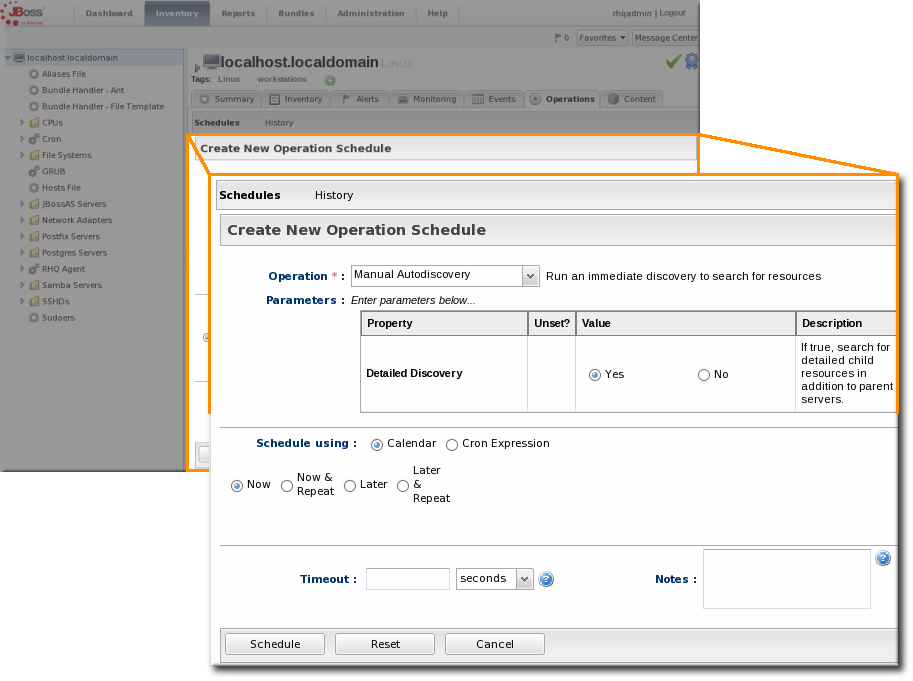
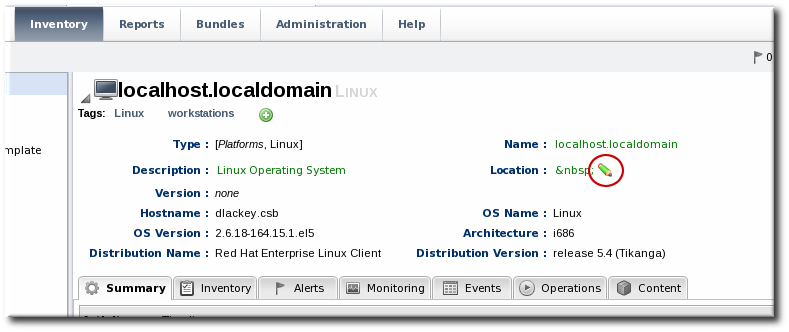
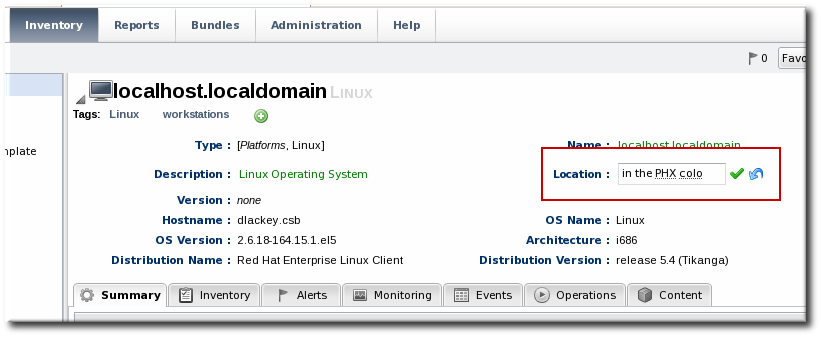
Figure 10. Editable Areas for a Resource Entry
1.2.6. Shortcuts in the UI
- The Message Center shows all notifications that have been sent by the JBoss ON server. This includes alerts, configuration changes, changes to the inventory, or error messages for the server or UI.
- The alerts area shows the total number of current alerts for all resources in the inventory.
- The Favorites button can be used to navigate to selected resources and groups quickly, while the little blue ribbon on resource pages can be used to add that resource to the favorites list.
- The resource available is shown as a green check mark if the resource is available and a red X if the resource is down.
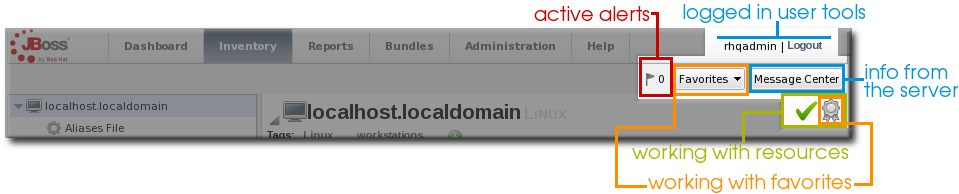
Figure 11. Shortcuts
1.3. Getting Notifications in the Message Center
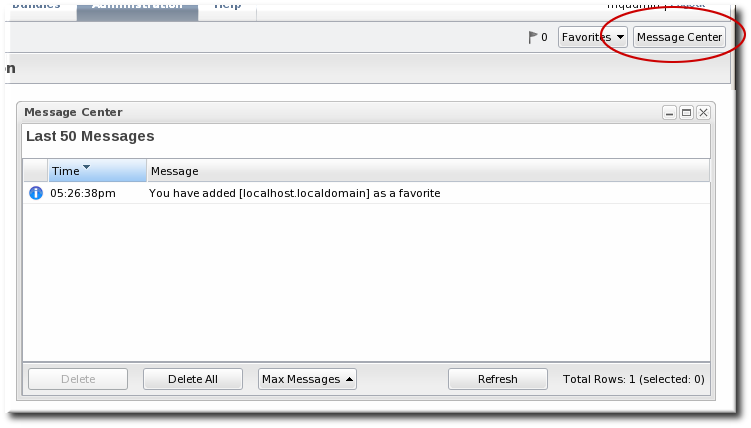
Figure 12. Message Center
1.4. Sorting and Changing Table Displays
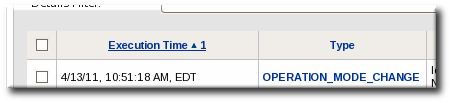
Figure 13. Basic Table Sorting on the Partition Events List
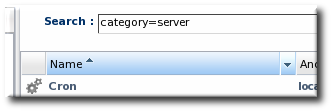
Figure 14. Basic Table Sorting on the Server Resources List
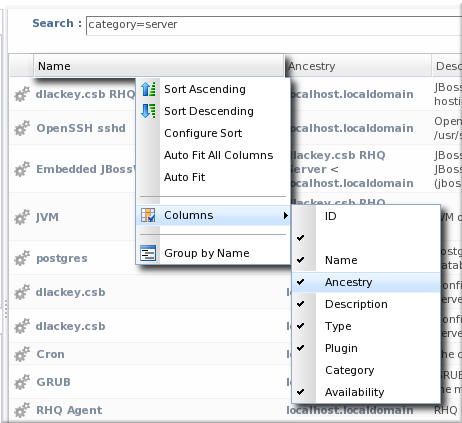
Figure 15. Advanced Table Sorting on the Server Resources List
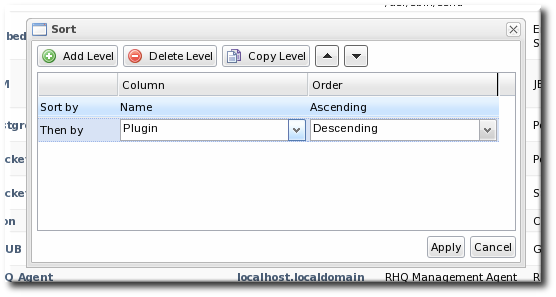
Figure 16. Changing the Sort Method
1.5. Customizing the Dashboard
Note
1.5.1. Editing Portlets

Figure 17. Portlet Icons
1.5.2. Adding and Editing Dashboards
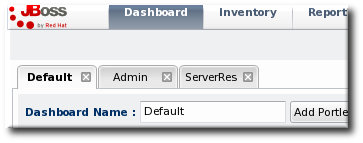
Figure 18. Tabbed Dashboards
- Click the New Dashboard button in the far right of the main Dashboard.
Note
The process of editing and adding Dashboards is very similar. The only difference is that to edit a Dashboard, you click the Edit Mode button. - The new Dashboard opens in the edit mode. Enter a name for the new Dashboard.
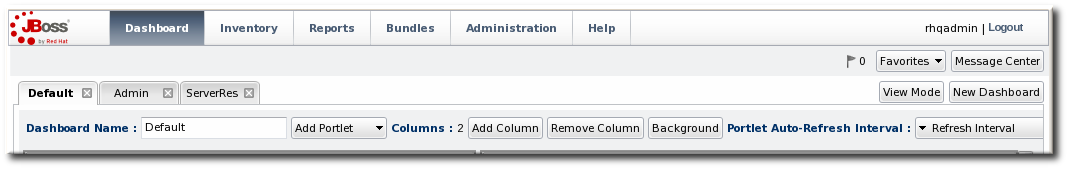
- Add the desired portlets to the Dashboard. If necessary, change the number of columns to fit the number of portlets.
1.6. Setting Favorites

Figure 19. Favorites Icon
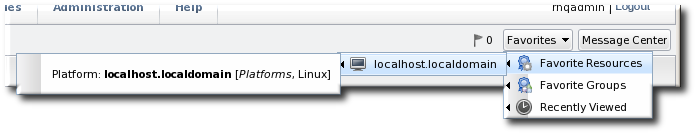
Figure 20. Favorites List
1.7. Deleting Entries
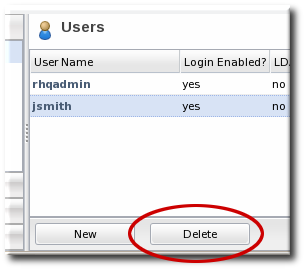
Figure 21. Delete Button in the Area Browser
Note
2. Dynamic Searches for Resources and Groups
2.1. About Search Suggestions
- Saved searches, which contain previous custom search strings and a count of resources which match that search
- Query searches, which provide prompts for available resource traits
- Text searches, which provide a list of resources based on some property in the resource which matches the text prompt
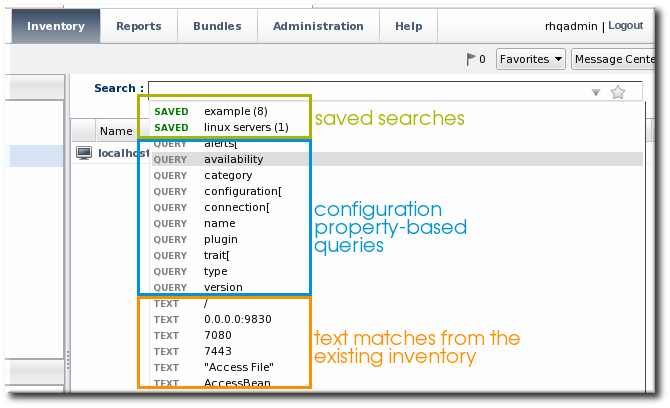
Figure 22. Types of Search Suggestions
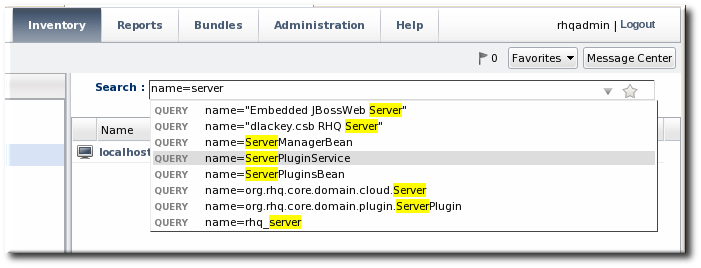
Figure 23. Highlighting Search Terms
2.2. About the Dynamic Search Syntax
[search_area].[search_property] operator value operator additional_search
resource. part of the search.
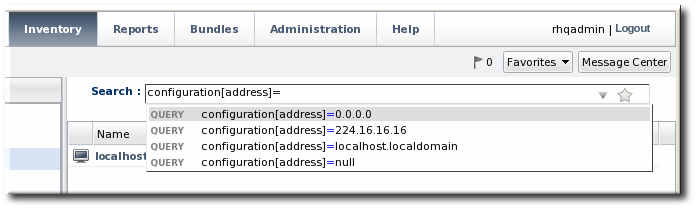
Figure 24. Searching by Resources Traits
2.2.1. Basic String Searches
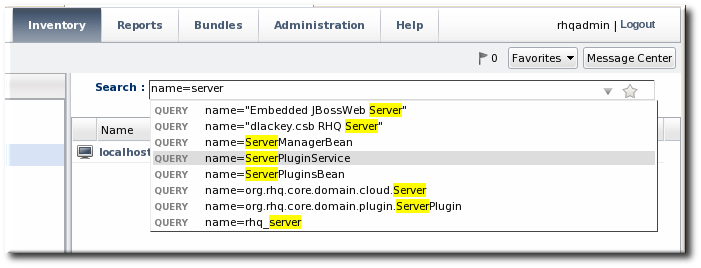
Figure 25. Matching the Search Term
agen has search suggestions that match (case-insensitive) every resource that has that string anywhere in its name, at the beginning (Agent Plugin Container), middle (RHQ Agent Launcher Script), or end (rhq_agent). Likewise, the results include every resource with that string, regardless of where it appears in the resource entry or attribute.
Important
*) or regular expressions.
postgres table myexampletable
"My Compatible Group" 'test box' plugin=jboss 123.4.5.6 trait[partitionName]='my example group' server.example.com
name="Production's Main Group"
'Hello world requires a closing single quote; Production's does not.
^) character sets that a search term must appear at the beginning of the result string. For example:
resource.id=^100$). For example:
script$
Table 1. String Operators
| Operator | Description |
|---|---|
| string | The string can occur anywhere in the result string. |
| ^string | The given string must appear at the beginning of the result value. |
| string$ | The given string must appear at the end of the result value. |
| ^string$ | The result must be an exact match of the given string, with no leading or trailing characters. |
Note
resource.trait[Database.startTime] = null
null will look for a resource or group with a value of the string null:
name = "null"
2.2.2. Property Searches
trait) is different than looking for an entry with an ID that includes 80 (id). The available properties are listed in Table 2, “Resource Search Contexts” and Table 3, “Group Search Contexts”.
Note
resource.type.plugin = Postgres
Important
connection, configuration, and trait use the internal property names for the property names (connection[property_name]) rather than the names used in the JBoss ON GUI.
Table 2. Resource Search Contexts
| Property | Description |
|---|---|
| resource.id | The resource ID number assigned by JBoss ON. |
| resource.name | The resource name, which is displayed in the UI. |
| resource.version | The version number of the resource. |
| resource.type.plugin | The resource type, defined by the plug-in used to manage the resource. |
| resource.type.name | The resource type, by name. |
| resource.type.category | The resource type category (platform, server, or service). |
| resource.availability | The resource availability, either UP or DOWN. |
| resource.pluginConfiguration[property-name] | The value of any possible configuration entry in a plug-in. |
| resource.resourceConfiguration[property-name] | The value of any possible configuration entry in a resource. |
| resource.trait[property-name] | The value of any possible measurement trait for a resource. |
Table 3. Group Search Contexts
| Property | Description |
|---|---|
| group.name | The name of the group. |
| group.plug-in | For a compatible group, the plug-in which defines the resource type for this group. |
| group.type | For a compatible group, the resource type for this group. |
| group.category | The resource type category (platform, server, or service). |
| group.kind | The type of group, either mixed or compatible. |
| group.availability | The availability of resource in the group, either UP or DOWN. |
Table 4. Search String Operators
| Operator | Description |
|---|---|
| = | Case-insensitive match. |
| == | Case-exact match. |
| != | Case-insensitive negative match (meaning, the value is not the string). |
| !== | Case-exact negative match (meaning, the value is not the string). |
2.2.3. Complex AND and OR Searches
postgres server myserver
postgres AND server AND myserver
|). For example:
postgres | jbossas
a | b c
Note
(a | b) (c | d)
(a) (b | (c d))
2.3. Saving, Reusing, and Deleting Dynamic Searches
- Run the search.

- Click the star in the right of the search bar. When the field comes up, enter the name for the new search.
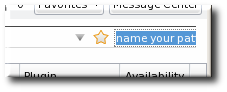 The search name is then displayed in green.
The search name is then displayed in green.


3. Managing the Resource Inventory
3.1. About the Inventory: Resources
3.1.1. Managed Resources: Platforms, Servers, and Services
- Platforms (operating systems)
- Servers
- Services
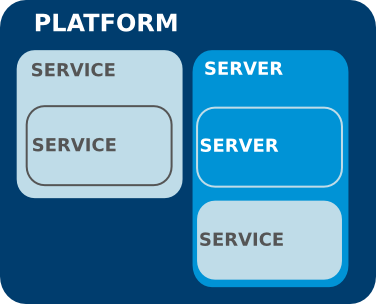
Figure 26. An Example Resource Hierarchy
- A resource can only have one parent.
- A server can be a child of a platform (such as JBoss AS on Linux) or another server (such as Tomcat embedded in JBoss AS).
- A service can be a child of a platform, a server (such as the JMS queue on JBoss AS), or another service (e.g. a table inside a database).
- Platforms, servers, and services can have many children services.
Note
Table 5. Default Resources Supported in JBoss ON
| Managed Platform | |||
| AIX | FreeBSD | HP-UX | Java |
| Linux | Mac OS X | Solaris | Windows |
| Managed Servers | |||
| Apache HTTP Server | JBoss BRMS (Drools) | JMS Manager Service (HornetQ) | Hibernate Services |
| Host Server | HTTPService | IIS Server | JBoss EAP/AS 4 and 5 |
| JBoss Cache Services 2.x and 3.x | JBoss ESB and ESB 5 | JMX Server | mod_cluster |
| Oracle | PostgreSQL | JBoss Developer Studio (ModeShape) | Tomcat Server |
| JBoss ON Agent | JBoss ON Server | ||
3.1.2. Content-Backed Resources
3.1.3. Resources in the Inventory Used by JBoss ON
rhq-agent-env.sh script. Adding these resources to the JBoss ON inventory allows JBoss ON to monitor and manage all of the agents and servers in the deployment.
3.2. Discovering Resources
3.2.1. Finding New Resources: Discovery
3.2.2. Running Discovery Scans Manually
discovery command at the agent command prompt:
- Start the agent terminal. Since the agent should already be running, using the
--nostartoption to start the agent terminal without attempting to start the agent process.# agentRoot/rhq-agent/bin/rhq-agent.sh --nostart
- In the agent terminal, run the
discoverycommand. Using the-foption runs a full discovery, for servers and services. Runningdiscoveryalone checks for servers only.> discovery -f
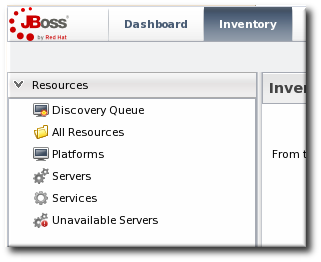
- Click the Inventory tab in the top menu.
- Select the platform resource in the Resources menu table on the left.
- Click the Operations tab.
- In the Schedules subtab, click the New button.
- Select the Manual Discovery operation from the drop-down menu, and select whether to run a detailed discovery (servers and services) or a simple discovery (servers only).
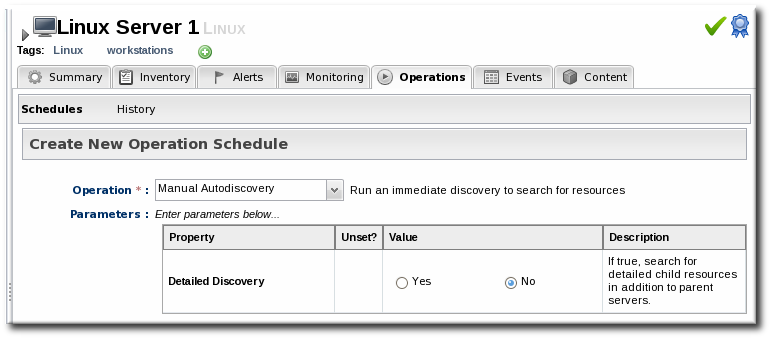
- In the Schedule area, select the radio button to run the operation immediately.

- Click the Schedule button to set up the operation.

3.2.3. Importing Resources from the Discovery Queue
- Click the Inventory tab in the top menu.
- In the Resources menu on the left, select Discovery Queue.
- Select the checkbox of the resources to be imported. Selecting a parent resource (such as a platform) gives the option to automatically import all of its children, too.
- Click the Import button at the bottom of the UI.
3.2.4. Ignoring Discovered Resources
Note
- Select Inventory from the top menu.
- Select the Discovery Queue item under the Resources menu on the left side of the screen.
- Select the checkbox of the resource to be ignored. Selecting a parent resource automatically selects all of its children.
- Click the Ignore button at the bottom of the page.
Note
3.3. Importing New Resources Manually
Note
- Click the Inventory tab in the top menu.
- Search for the parent resource of the new resource.Section 2, “Dynamic Searches for Resources and Groups” has information on searching for resources using dynamic searches.
- Click the Inventory tab of the parent resource.
- Click the Import button in the bottom of the Inventory tab, and select the type of child resource. The selection menu lists the possible types of child resources for that parent.
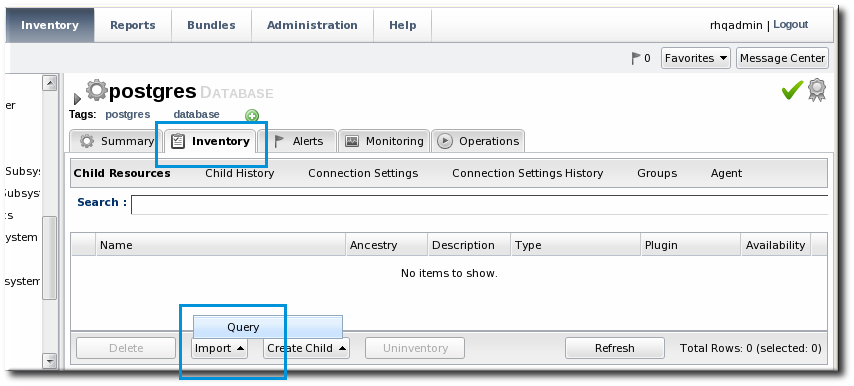
- Fill in the properties to identify and connect to the new resource. Each resource type in the system has a different set of required properties.

3.4. Configuring Tomcat/EWS Servers for Discovery (Windows)
- Run
regedit. - Navigate to Java preferences key for the Tomcat server,
HKEY_LOCAL_MACHINE\SOFTWARE\Apache Software Foundation\Procrun2.0\TomcatVer#\Parameters\Java. - Edit the Options attribute, and add these parameters:
-Dcom.sun.management.jmxremote.port=9876 -Dcom.sun.management.jmxremote.ssl=false -Dcom.sun.management.jmxremote.authenticate=false
- Restart the Tomcat service.
3.5. Creating Child Resources
Note
- Click the Inventory tab in the top menu.
- Search for the parent resource of the new resource.Section 2, “Dynamic Searches for Resources and Groups” has information on searching for resources using dynamic searches.
- Click the Inventory tab of the parent resource.
- Click the Create Child button in the bottom of the Inventory tab, and select the type of child resource. The selection menu lists the possible types of child resources for that parent.
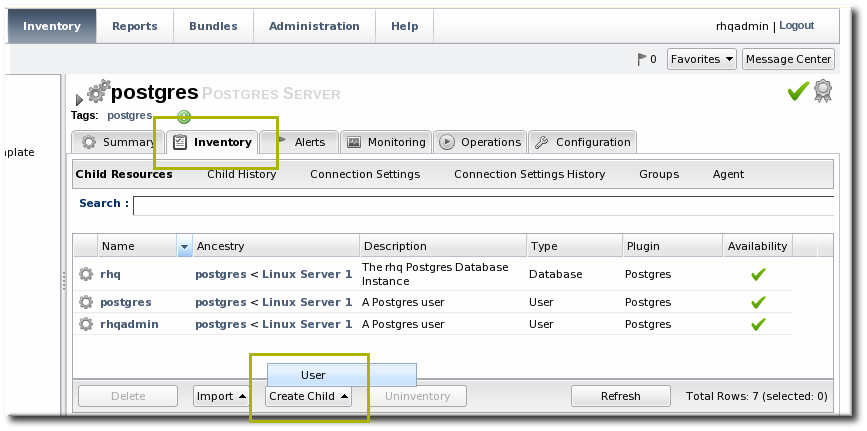
- Give the name and description for the new resource.

- Fill in the properties to identify and connect to the new resource. Each resource type in the system has a different set of required properties.

3.6. Viewing and Editing Resource Information
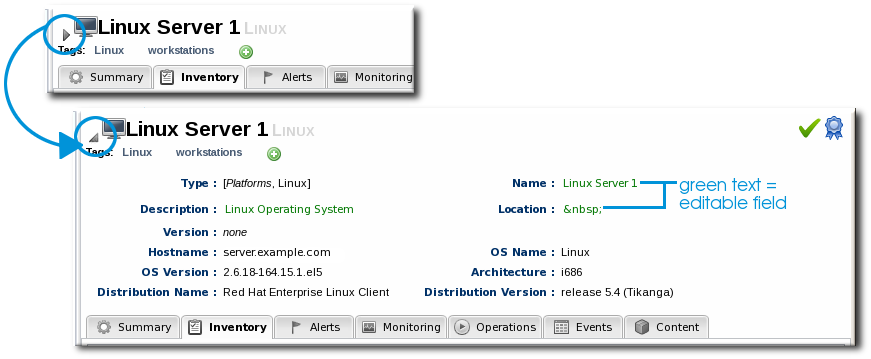
Figure 27. Expanding Resource Entry Details
3.7. Removing Resources from the Inventory
Note
3.7.1. Uninventorying through the Parent Inventory
- Click the Inventory tab in the top menu.
- Search for the parent resource of the new resource.Section 2, “Dynamic Searches for Resources and Groups” has information on searching for resources using dynamic searches.
- Click the Inventory tab for the parent resource.
- Click on the line of the child resource to uninventory. To select multiple entries, use the Ctrl key.

- Click the Uninventory button.
- When prompted, confirm that the resource should be uninventoried.

3.7.2. Uninventorying through a Group Inventory
- In the Inventory tab in the top menu, select the compatible or mixed groups item in the Groups menu on the left.

- Click the name of the group.
- Open the Inventory tab for the group, and open the Members submenu.
- Click on the line of the group member to uninventory. To select multiple entries, use the Ctrl key.

- Click the Uninventory button.
- When prompted, confirm that the resource should be uninventoried.

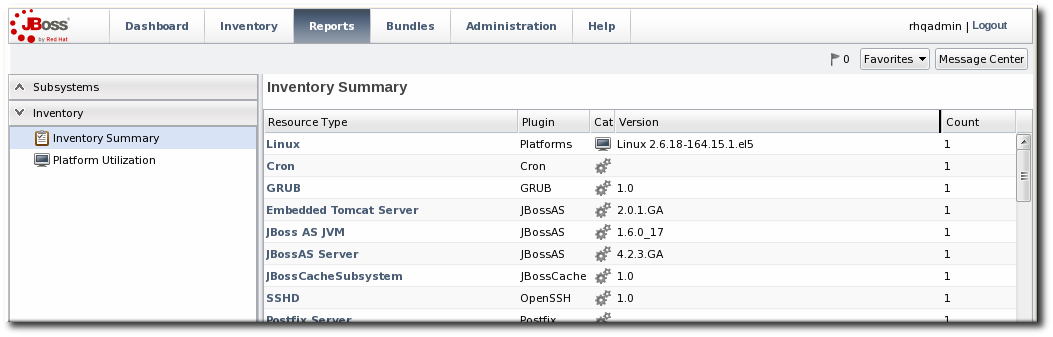
3.8. Getting Inventory Reports
- Resource type
- The JBoss ON server plug-in which manages the resource
- The JBoss ON category for the resource (platform, server, or service)
- The version number of the resource type; for example, for the Linux resource type, there can be a Linux 2.6.18-164.15.1.el5 version
- The total number of resources of that type in the inventory
- In the top menu, click the Reports tab.
- In the Inventory menu box in the menu table on the left, select the Inventory Summary report.
Note
4. Managing Groups
4.1. About Groups
Table 6. Types of Groups
| Type | Description | Static or Dynamic |
|---|---|---|
| Mixed groups | Contains resources of any resource type. There is no limit to how many or what types of resources can be placed into a mixed group. Mixed groups are useful for granting access permissions to users for a set of grouped resources. | Static |
| Compatible groups | Contains only resources of the same type. Compatible groups make it possible to perform an operation against every member of the group at the same time, removing the need to individually upgrade multiple resources of the same type, or perform other operations one at a time on resources across the entire enterprise. | Static |
| Recursive groups | Contains all the descendant, or child, resources of resources within the group. Recursive groups show both the primary member availability and the child resource availability. | Static (members) and dynamic (children) |
| Autogroups | Shows every resource as part of a resource hierarchy with the platform at the top, and child and descendant resources below the platform. Child resources of the same type are automatically grouped into an autogroup. | Dynamic |
4.1.1. Dynamic and Static Groups
4.1.2. About Autogroups
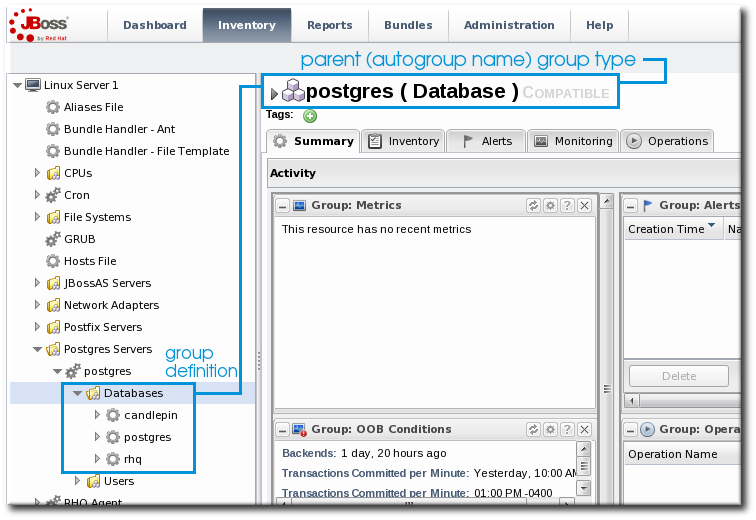
Figure 28. PostgreSQL Autogroup
4.1.3. Comparing Compatible and Mixed Groups
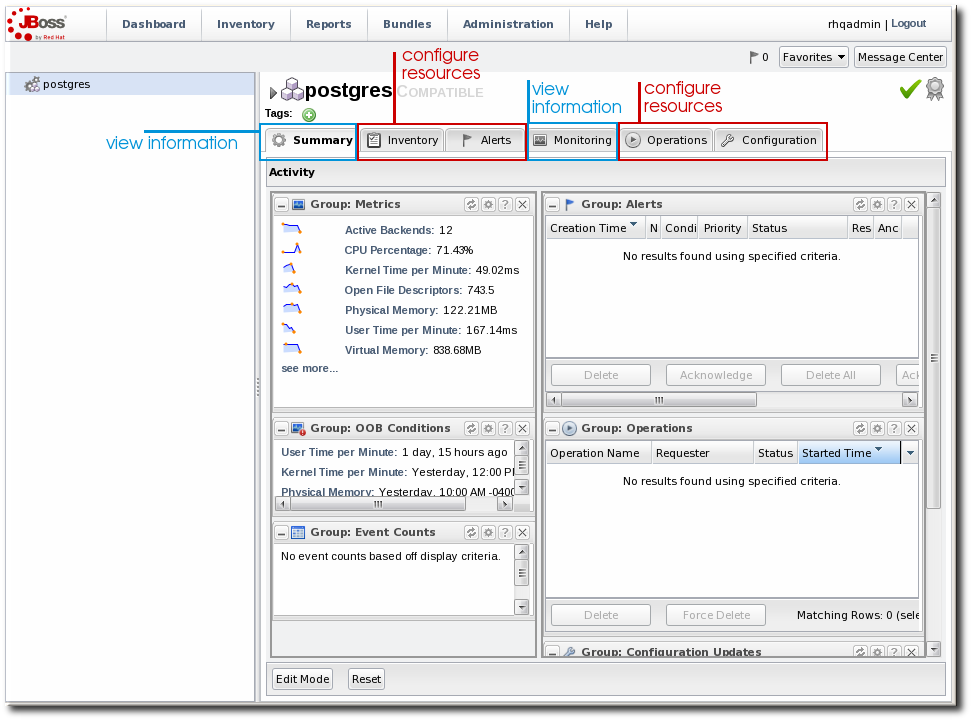
Figure 29. Compatible Group Entry
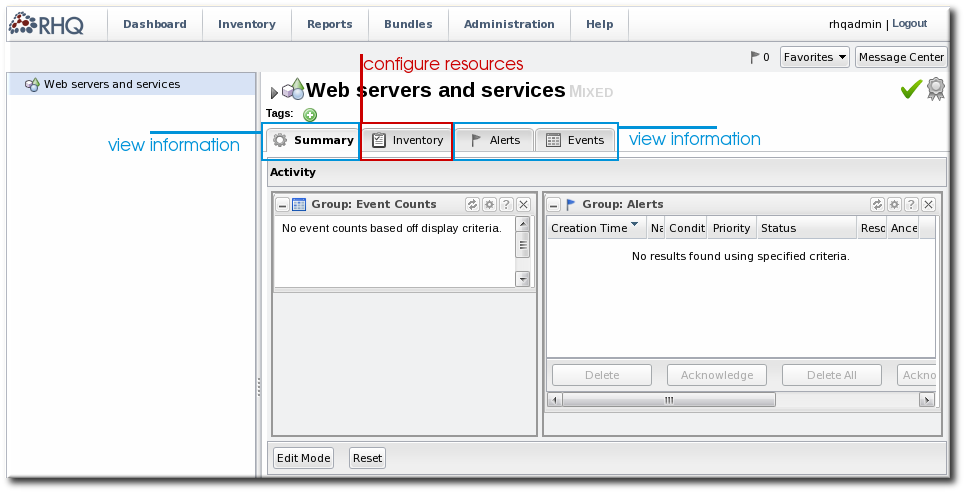
Figure 30. Mixed Group Entry
4.2. Creating Dynamic Groups
Note
4.2.1. About Dynamic Groups Syntax
4.2.1.1. General Expression Syntax
expression 1 exprA1 exprA2 groupby exprB1 groupby exprB2 expression 2 exprA2 exprA1 groupby exprB2 groupby exprB1
Note
Table 7. Dynamic Group Properties
| Type | Supported Attributes | ||||||
|---|---|---|---|---|---|---|---|
| Related to the resource itself | |||||||
|
resource
|
| ||||||
| Related to the resource type | |||||||
|
resourceType
|
| ||||||
| Related to the resource configuration | |||||||
|
plug-inConfiguration
|
Any plugin configuration property
| ||||||
|
resourceConfiguration
|
Any resource configuration property
| ||||||
| Related to the resource monitoring data | |||||||
|
traits
|
Any monitoring trait
| ||||||
|
availability
|
The current state, either UP or DOWN
| ||||||
resource.attribute, then it applies to the resource which will be a member of the group. However, it is possible to use an attribute in an ancestor or child entry to identify a group member recursively.
resource.id = 10001
resource.parent:
resource.parent.id = 10001
- resource
- resource.child
- resource.parent
- resource.grandParent
4.2.1.2. Simple Expressions
resource.attribute[string-expression] = value
resource.parent.type.category = Platform
resource.trait is the generic resource attribute, and a sub-attribute like partitionName identifies the actual parameter.
empty keyword searches for resources which have a specific attribute with a null value:
empty resource.attribute[string-expression]
empty keyword is used, then there is no value given with the expression.
not empty keyword, which looks for every resource with that attribute, regardless of the attribute value, as long as it is not null. As with the empty keyword, there is no reason to give a value with the expression, since every value matches the expression.
not empty resource.attribute[string-expression]
4.2.1.3. Pivot Expressions
groupby keyword:
groupby resource.attribute
parent.name attribute creates a unique group based on every parent resource.
groupby resource.parent.name
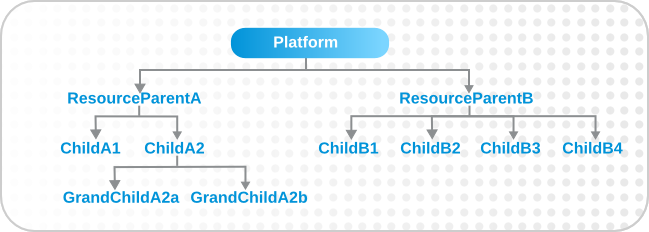
Figure 31. Resources and Parents
4.2.1.4. Compound Expressions
resource.parent.type.category = Platform
resource.parent.type.category = Platform resource.name.contains = JBossAS
groupby resource.type.plugin groupby resource.type.name groupby resource.parent.name
resource.type.category = server groupby resource.type.plugin groupby resource.type.name groupby resource.parent.name
resource.type.plugin = JBossAS resource.type.name = JBossAS Server empty resource.pluginConfiguration[principal]
4.2.1.5. Dynagroup Expression Examples
Table 8. Dynagroup Examples
| Description | Expression |
|---|---|
| JBoss clusters |
resource.type.plugin = JBossAS resource.type.name = JBossAS Server groupby resource.trait[partitionName] |
| Each operating system type |
resource.type.plugin = Platforms resource.type.category = PLATFORM groupby resource.type.name |
| All autogroups
Note
This could create a large number of groups in large inventories.
|
groupby resource.type.plugin groupby resource.type.name groupby resource.parent.name |
| Just raw measurement tables |
resource.type.plugin= Postgres resource.type.name = Table resource.parent.name = rhq Database resource.name.contains = rhq_meas_data_num_ |
| Just agents configured with multi-cast server detection |
resource.type.plugin= RHQAgent resource.type.name = RHQ Agent resource.resourceConfiguration[rhq.communications.multicast-detector.enabled] = true |
| Just Windows platforms with event tracking |
resource.type.plugin= Platforms resource.type.name = Windows resource.pluginConfiguration[eventTrackingEnabled] = true |
| JBoss AS servers grouped by machine |
groupby resource.parent.trait[Trait.hostname] resource.type.plugin = JBossAS resource.type.name = JBossAS Server |
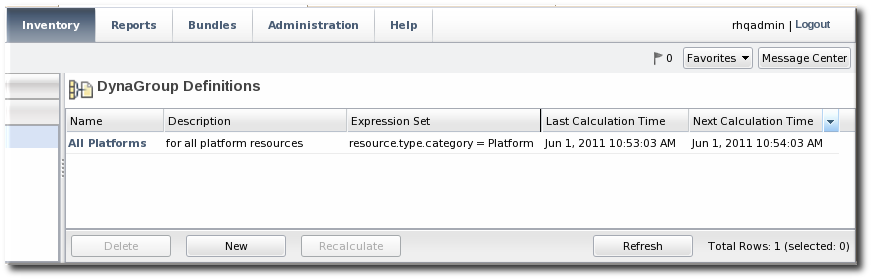
4.2.2. Creating Dynamic Groups
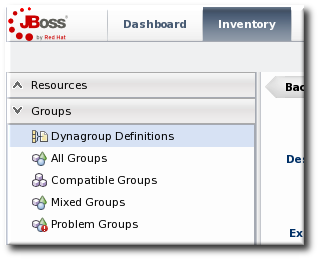
- Click the Inventory tab in the top menu.
- In the Groups menu box on the left, click the Dynagroup Definitions link.
- Click the New button to open the dynamic group definition form.
- Fill in the name and description for the dynamic group. The name can be important because it is prepended to any groups created by the definition, as a way of identifying the logic used to create the group.

- Fill in the search expressions. This can be done by entering expressions directly in the Expression box or by using a saved expression.Saved expressions are have a wizard to help build and validate the expressions. To create a saved expression, click the green button by the drop-down menu. Several options for the expression are active or inactive depending on the other selections; this prevents invalid expressions.
 The Expression box at the top shows the currently created expression.
The Expression box at the top shows the currently created expression. - After entering the expressions, set whether the dynamic group is recursive.
- Set an optional recalculation interval. By default, dynamic groups do not recalculate their members automatically, meaning the recalculation value is set to 0. To recalculate the group membership, set the Recalculation interval to the time frequency, in milliseconds.
Note
Recalculating a group definition across large inventories could be resource-intensive for the JBoss ON server, so be careful when setting the recalculation interval. For large inventories, set a longer interval, such as an hour, to avoid affecting the JBoss ON server performance.
4.2.3. Recalculating Group Members
- Click the Inventory tab in the top menu.
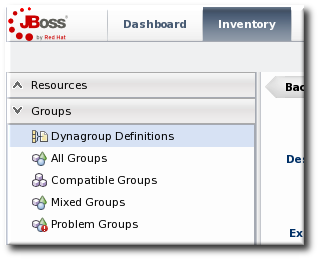
- In the Groups menu on the left, click the Dynagroup Definitions link.
- In the list of dynagroups, select the row of the dynagroup definition to calculate.
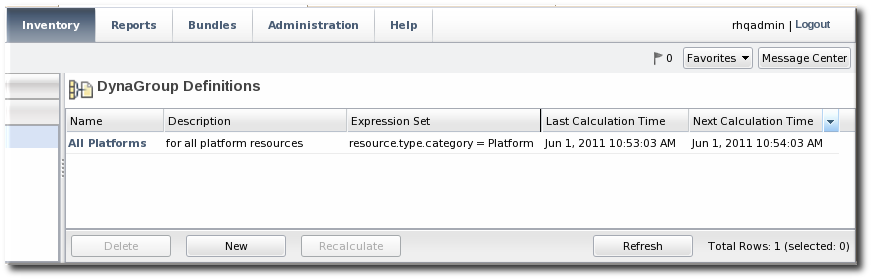
- Click the Recalculate button at the bottom of the table.
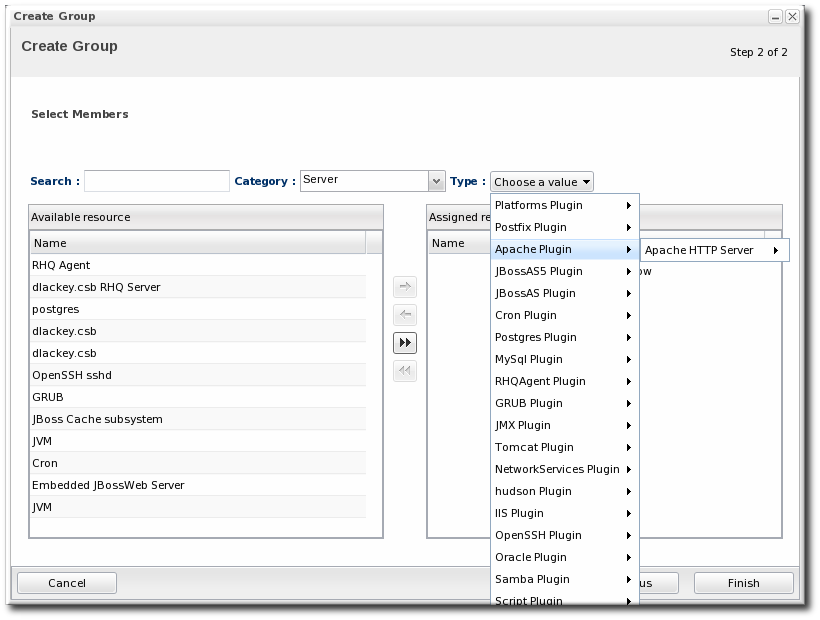
4.3. Creating Groups
- Click the Inventory tab in the top menu.
- In the Groups box in the left menu, select the type of group to create, either compatible or mixed.Compatible groups have resources all of the same type, while mixed groups have members of different types. The differences in the types of members means that there are different ways that compatible and mixed groups can be managed, as covered in Section 4.1.3, “Comparing Compatible and Mixed Groups”.

- Enter a name and description for the group.
 Marking mixed groups recursive can make it easier to manage resources, particularly when setting role access controls. For example, administrators can grant users access to the mixed group and automatically include any child resources of the member resources.
Marking mixed groups recursive can make it easier to manage resources, particularly when setting role access controls. For example, administrators can grant users access to the mixed group and automatically include any child resources of the member resources.Note
Be very cautious before marking a compatible group as a recursive group. Recursive groups automatically import all children of the members, and if the children are a different resource type than the parent, then the compatible group becomes a mixed group. This limits the management options for the group because group operations, metrics, and configuration changes are only available for compatible groups. - Select the group members. It is possible to filter the choices based on name, type, and category.
4.4. Changing Group Membership
- In the Inventory tab in the top menu, select the compatible or mixed groups item in the Groups menu on the left.

- Click the name of the group.
- Open the Inventory tab for the group, and open the Members submenu.
- Click the Update Membership button at the bottom of the page.
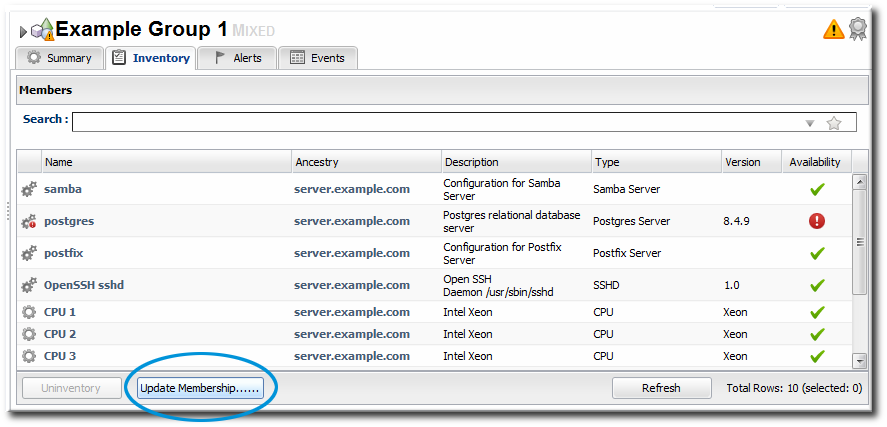
- Select the resources to add to the group from the box on the left; to remove members, select them from the box on the right. Use the arrows to move the selected resources. To select multiple resources, use Ctrl+click.
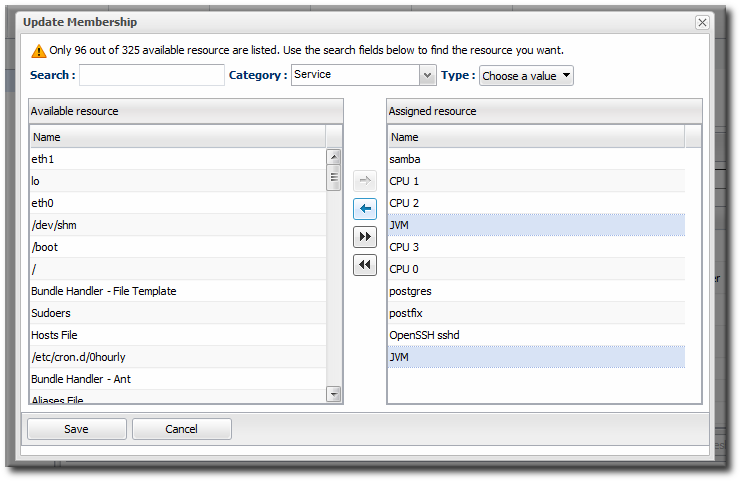
- Click the Save button.
4.5. Editing Compatible Group Connection Properties
- If all of the resources in the group have identical values for a property, the group connection property is that exact value.
- If even one resource has a different value than the rest of the resources in the group, that property will have a special marker value of ~ Mixed Values ~.
- In the Inventory tab in the top menu, select the Compatible Groups item in the Groups menu on the left.

- Click the name of the compatible group.
- Open the Inventory tab for the group, and click the Connection Settings sub-item.
- To edit a property, click the green pencil by the field.

- To change all resources to the same value, click the Unset checkbox for the field Set all values to.... To change a specific resource, click the Unset checkbox for that resource and then give the new value.

Note
5. Creating User Accounts
5.1. Managing the rhqadmin Account
rhqadmin. This superuser has the default password rhqadmin.
Note
rhqadmin account cannot be deleted, even if other superuser accounts are created. Additionally, the role assignments for rhqadmin cannot be changed; it is always a superuser account.
Important
- Click the Administration tab in the top menu.
- In the Security table on the left, select Users.

- Click the name of
rhqadmin. - In the edit user form, change the password to a new, complex value.

5.2. Creating a New User
- Click the Administration tab in the top menu.
- In the Security table on the left, select Users.

- Click the NEW button at the bottom of the list of current users.
- Fill in description of the new user. The Enable Login value must be set to Yes for the new user account to be active.

- Select the required role from the Available Roles area, and then click the arrow pointing to the Assigned Roles to assign the role.
- Click the Save button to save the new user with the role assigned.
5.3. Editing User Entries
- Click the Administration tab in the top menu.
- From the Security menu, select Users.
- Click the name of the user whose entry will be edited.
- In the edit user form, change whatever details need to be changed, and save.

5.4. Disabling User Accounts
- Click the Administration tab in the top menu.
- In the Security table on the left, select Users.

- Click the name of the user whose entry will be edited.
- In the edit user form, change the Enable Login radio button to No.

- Click the Save button to save the new user with the role assigned.
5.5. Changing Role Assignments for Users
- Click the Administration tab in the top menu.
- From the Security menu, select Users.

- Click the name of the user to edit.
- To add a role to a user, select the required role from the Available Roles area, click the arrow pointing to the Assigned Roles area. To remove a role, select the assigned role on the right and click the arrow pointing to the left.
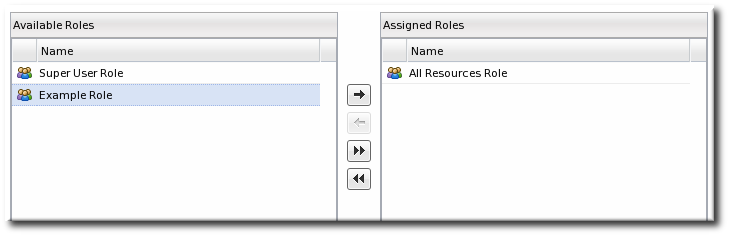
- Click Save to save the role assignments.
6. Managing Roles and Access Control
6.1. About Security in JBoss ON: Roles and Access Control
- Global permissions apply to JBoss ON server configuration. This covers administrative tasks, like creating users, editing roles, creating groups, importing resources into the inventory, or changing JBoss ON server properties.
- Resource-level permissions apply to actions that a user can perform on resources in the JBoss ON inventory. These cover actions like creating alerts, configuring monitoring, and changing resource configuration. Resource-level permissions are tied to the subsystem areas within JBoss ON.
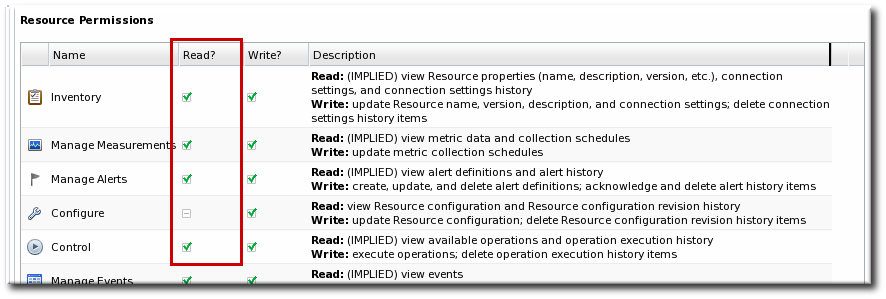
Figure 32. Read Access Option
Note
Table 9. JBoss ON Access Control Definitions
| Access Control Type | Description |
|---|---|
| Global - Security | Equivalent to a superuser. Security permissions grant the user the rights to create and edit any entries in JBoss ON, including other users, roles, and resources, to change JBoss ON server settings, and to control inventory.
Warning
The Security access control level is extremely powerful, so be cautious about which users are assigned it. Limit the number of superusers to as few as necessary.
|
| Global - Inventory | Allows any operation to be performed on any JBoss ON resource, including importing new resources. |
| Global - Settings | Allows a user to add or modify any settings in the JBoss ON server configuration itself. This includes operations like deploying plug-ins or using LDAP authentication. |
| Global - Bundles | Allows a user to upload and manage bundles (packages) used for provisioning resources. |
| Global - Repositories | Allows a user to access any configured repository, including private repositories and repositories without specified owners. Users with this right can also associated content sources with repositories. |
| Resource - Modify | Allows a user to change the resource definition entry in JBoss ON. This does not grant rights to edit the resource configuration. |
| Resource - Delete | Allows the user to delete the resource from the inventory. |
| Resource - Create Child | Allows the user to manually assign a child resource to another resource. |
| Resource - Alerts | Allows the user to create alerts and notifications on a resource. Configuring new alert senders changes the server settings and is therefore a function of the global Settings permissions. |
| Resource - Measurements | Allows the user to configure monitoring settings for the resource. |
| Resource - Content | Allows the user to manage content providers and repositories that are available to resources. |
| Resource - Control | Allows a user to run operations (which are also called control actions) on a resource. |
| Resource - Configure | Allows users to change the configuration settings on the resource through JBoss ON.
Note
The user still must have adequate permissions on the resource to allow the configuration changes to be made.
|
Note
- A superuser role provides complete access to everything in JBoss ON. This role cannot be modified or deleted. The user created when the JBoss ON server was first installed is automatically a member of this role.
- An all resources role exists that provides full permissions to every resource in JBoss ON (but not to JBoss ON administrative functions like creating users). This is a useful role for IT users, for example, who need to be able to change the configuration or set up alerts for resources managed by JBoss ON but who don't require access over JBoss ON server or agent settings.
6.2. Creating a New Role
Note
- Create any resources groups which will be associated with the role. Creating groups is described in Section 4.3, “Creating Groups”.By default, JBoss ON uses only resource groups to associate with a role, and these are required. However, optional user groups from an LDAP directory can also be assigned to a role, so that the group members are automatically treated as role members. LDAP groups must be configured in the server settings, as described in Section 7.5, “Associating LDAP User Groups to Roles in JBoss ON”.
- In the top menu, click the Administration tab.

- In the Security menu table on the left, select the Roles item.

- The list of current roles comes up in the main task window. Click the New button at the bottom of the list.
- Give the role a descriptive name. This makes it easier to manage permissions across roles.
- Global permissions grant permissions to areas of the JBoss ON server and configuration.
- Resource permissions grant permissions for managing resources.
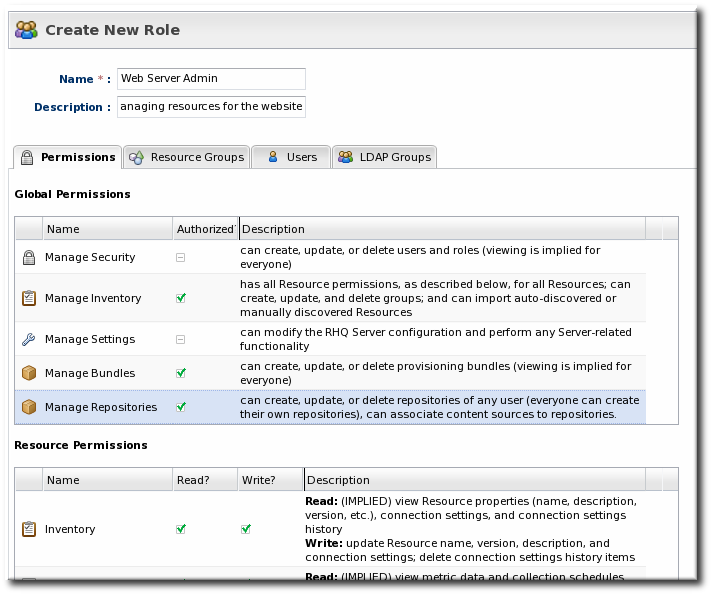 The specific access permissions are described in Table 9, “JBoss ON Access Control Definitions”.
The specific access permissions are described in Table 9, “JBoss ON Access Control Definitions”.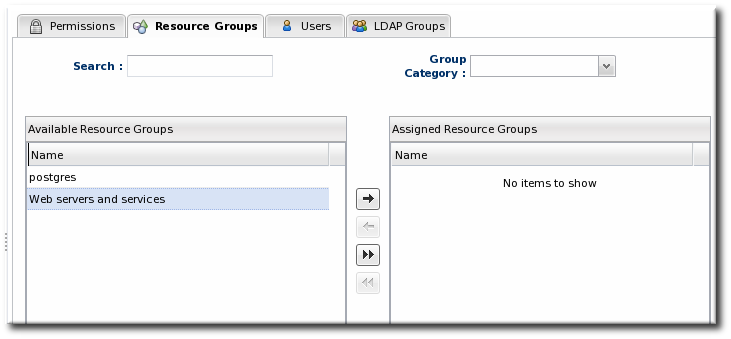 Move the required groups from the Available Resource Groups area on the left to the Assigned Resource Groups on the right as required.
Move the required groups from the Available Resource Groups area on the left to the Assigned Resource Groups on the right as required.- At the bottom, click the Save button.
- Select the Users tab to assign users to the role.
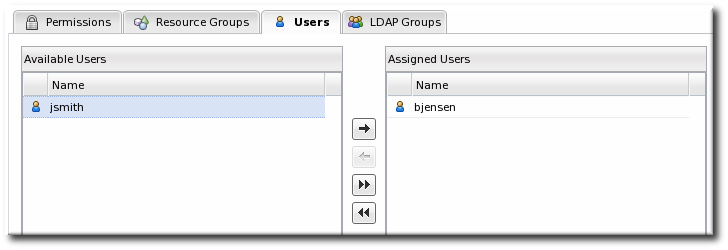 Move the required user from the Available Users area on the left, to the Assigned Users on the right as required.
Move the required user from the Available Users area on the left, to the Assigned Users on the right as required. - Click the arrow in the upper right to close the create window.
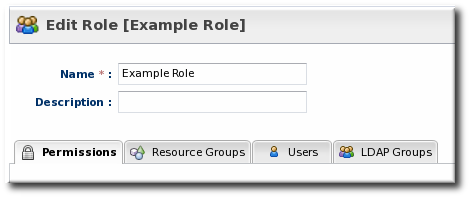
6.3. Editing Roles
- In the Security menu table on the left, select the Roles item, and click the name of the role to edit.

- Go through the role's tabs and change the configuration as desired.
7. Integrating LDAP Services for Authentication and Authorization
Important
7.1. Supported Directory Services
- Red Hat Directory Server 8.1 and 8.2
- Microsoft Active Directory 2003 and 2008
7.2. How JBoss ON Uses LDAP for Authentication
Warning
Note
JONUser=true, which can make it easier and more precise to locate entries.
Note
Integrating LDAP directories introduces another area where users can be created and managed and where the membership of roles can be changed. On the one hand, this can make managing users much easier, especially by allowing existing users to register themselves seamlessly and by automatically updating role membership. However, because users can still be created in JBoss ON and added manually to JBoss ON, user and role management can become messy.
jsmith) and password, but is improperly assigned the JBoss ON role membership of LDAP user John Smith (LDAP UID jsmith) because her JBoss ON user ID was the same as his LDAP user ID, and her account was incorrectly mapped to his LDAP account and, therefore, his LDAP group membership.
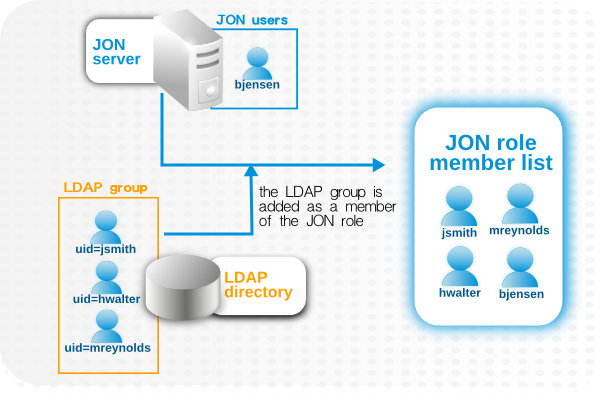
Figure 33. LDAP Groups, JBoss ON Roles, and Role Members
- Only create regular user accounts in one place. If LDAP should be used for authentication, then only add or delete user accounts in the LDAP directory.
- Ideally, limit JBoss ON user accounts to special, administrative users and rely on the LDAP directory for regular accounts.
- Try to design roles around LDAP groups, meaning that JBoss ON user accounts in those roles should be limited to admin accounts or avoided altogether.
7.3. Configuring LDAP User Authentication
- In the top menu, click the Administration tab.

- In the Configuration menu table on the left, select the System Settings item.

- Jump to the LDAP Configuration Properties area.
- Check the Use LDAP Authentication checkbox so that JBoss ON will use the LDAP user directory as its identity store.
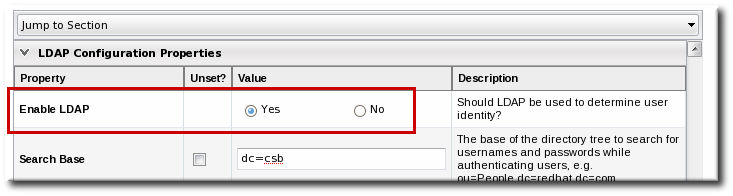
- Configure the connection settings to connect to the specific LDAP directory.
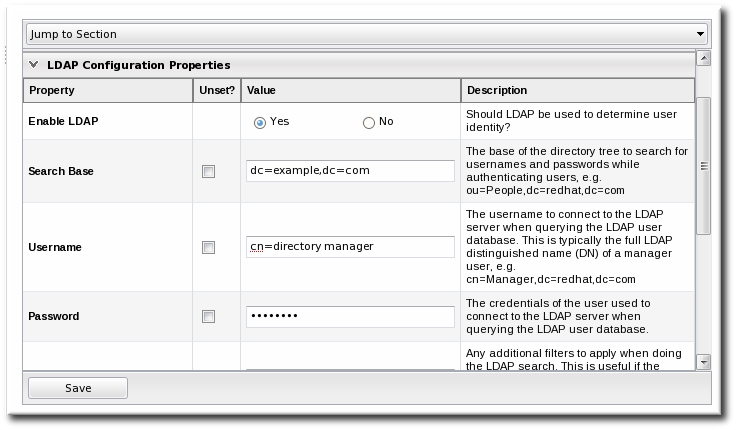
- Give the LDAP URL of the LDAP server. This has the format
ldap://hostname[:port]. For example:ldap://server.example.com:389
By default, this connects to the localhost over port 389 (standard LDAP port) or 636 (secure LDAP port, if SSL is selected). - To use a secure connection, check the Use SSL checkbox. When using SSL, make sure that the LDAP directory is actually running over SSL, and make sure that the connection URL points to the appropriate SSL port and protocol:
ldap
s://server.example.com:636 - Give the bind credentials to use to connect to the server. The username is the full LDAP distinguished name of the user as whom JBoss ON binds to the directory.
Note
The user must exist in the LDAP directory before configuring the LDAP settings in JBoss ON. Otherwise, login attempts to the JBoss ON server will fail.Also, make sure that the JBoss ON user has appropriate read and search access to the user and group subtrees in the LDAP directory.
- Set the search parameters that JBoss ON uses when searching the LDAP directory for matching user entries.
- The search base is the point in the directory tree where the server begins looking for entries. If this is used only for user authentication or if all JBoss ON-related entries are in the same subtree, then this can reference a specific subtree:
ou=user,ou=JON,dc=example,dc=com
If the users or groups are spread across the directory, then select the base DN:dc=example,dc=com
- Optionally, set a search filter to use to search for a specific subset of entries. This can improve search performance and results, particularly when all JBoss ON-related entries share a common LDAP attribute, like a custom
JonUserattribute. The filter can use wild cards (objectclass=*) or specific values (JonUser=true). - Set the LDAP naming attribute; this is the element on the farthest left of the full distinguished name. For example, in
uid=jsmith,ou=people,dc=example,dc=com, the far left element isuid=jsmith, and the naming attribute isuid.The default naming attribute in Active Directory iscn. In Red Hat Directory Server, the default naming attribute isuid.
- Save the LDAP settings.
Note
The Group Filter and Member Property fields aren't required for user authentication. They're used for configuring LDAP groups to be assigned to roles, as in Section 7.5, “Associating LDAP User Groups to Roles in JBoss ON”.
7.4. How JBoss ON Roles Work with LDAP User Groups
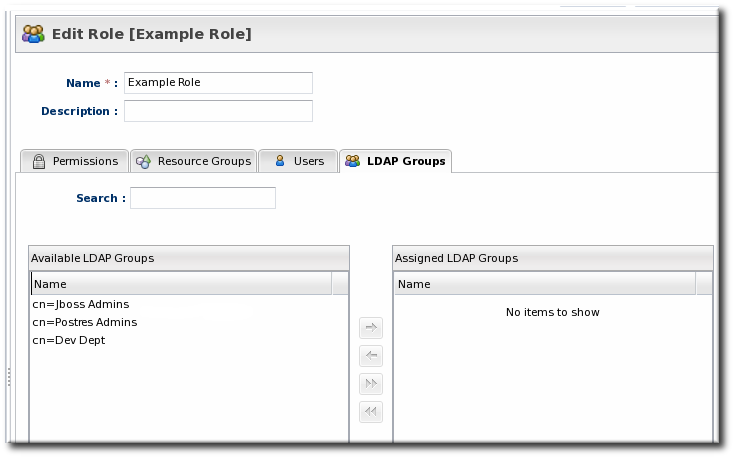
Figure 34. Groups Assigned to a Role
- An LDAP directory server connection has to be configured.
- There has to be an LDAP attribute given to search for group entries.For Active Directory, this is generally the
groupobject class. For Red Hat Directory Server, this is generallygroupOfUniqueNames. Other standard object classes are available, and it is also possible to use a custom, even JBoss ON-specific, object class. - There has to be an LDAP attribute given to identify members in the group.Common member attributes are
memberanduniqueMember.
(&(group_filter)(member_attribute=user_DN))
member attribute on an Active Directory group:
ldapsearch -h server.example.com -x -D "cn=Administrator,cn=Users,dc=example,dc=com" -W -b "dc=example,dc=com" -x '(&(objectclass=group)(member=CN=John Smith,CN=Users,DC=example,DC=com))'uniqueMember attribute on groupOfUniqueNames groups more commonly than member and group. For example:
/usr/lib64/mozldap6/ldapsearch -D "cn=directory manager" -w secret -p 389 -h server.example.com -b "ou=People,dc=example,dc=com" -s sub "(&(objectclass=groupOfUniqueNames)(uniqueMember=uid=jsmith,ou=People,dc=example,dc=com))"Note
7.5. Associating LDAP User Groups to Roles in JBoss ON
- In the top menu, click the Administration tab.

- In the Configuration menu table on the left, select the System Settings item.

- Jump to the LDAP Configuration Properties area.
- Set up the LDAP connections, as described in Section 7.3, “Configuring LDAP User Authentication”. It is not required that the LDAP directory be used as the identity store in order to configure LDAP authorization, but it is recommended.
- Set the parameters to use for the server to use to search for LDAP groups and their members.The search filter that JBoss ON constructs looks like this:
(&(group_filter)(member_attribute=user_DN))
- The Group Search Filter field sets how to search for the group entry. This is usually done by specifying the type of group to search for through its object class:
(objectclass=groupOfUniqueNames)
- The Group Member Filter field gives the attribute that the specified group type uses to store member distinguished names. For example:
uniqueMember
The user_DN is dynamically supplied by JBoss ON when a user logs into the UI. - Save the LDAP settings.
8. Document Information
8.1. Giving Feedback
- Select the Other products group.
- Select RHQ Project from the list.
- Set the component to Documentation.
- Set the version number to 3.0.
- For errors, give the page number (for the PDF) or URL (for the HTML), and give a succinct description of the problem, such as incorrect procedure or typo.For enhancements, put in what information needs to be added and why.
- Give a clear title for the bug. For example,
"Incorrect command example for setup script options"is better than"Bad example".
8.2. Document History
| Revision History | |||
|---|---|---|---|
| Revision 3.0.1-5 | 2013-10-31 | Rüdiger Landmann | |
| |||
| Revision 3.0.1-0 | March 18, 2012 | Ella Deon Lackey | |
| |||
| Revision 3.0-0 | December 7, 2011 | Ella Deon Lackey | |
| |||
Index
A
- access controls, About Security in JBoss ON: Roles and Access Control
- about read rights, About Security in JBoss ON: Roles and Access Control
- applying to resources, Creating a New Role
- assigning to users, Changing Role Assignments for Users
- changing on roles, Editing Roles
- list of permissions, About Security in JBoss ON: Roles and Access Control
- users, Creating User Accounts
- authentication
- and LDAP, Configuring LDAP User Authentication
- configuring LDAP, Configuring LDAP User Authentication
- storing credentials, How JBoss ON Uses LDAP for Authentication
- authorization
- for LDAP groups and roles, How JBoss ON Roles Work with LDAP User Groups
B
- boundary characters
- in searches, Basic String Searches
D
- discovery
- ignoring resources, Ignoring Discovered Resources
- importing, Importing Resources from the Discovery Queue
- manual, Running Discovery Scans Manually
- resources, Importing Resources from the Discovery Queue
- dynamic search
- groups and resources, Dynamic Searches for Resources and Groups
- null, Basic String Searches
- saving, reusing, and deleting, Saving, Reusing, and Deleting Dynamic Searches
- syntax, About the Dynamic Search Syntax
- using quotation marks, Basic String Searches
G
- groups
- and roles, About Security in JBoss ON: Roles and Access Control
- assigning to roles, Creating a New Role
- changing role assignments, Editing Roles
- dynamic search, Dynamic Searches for Resources and Groups
- empty groups, General Expression Syntax
- overview, Managing Groups
- search context, Property Searches
I
- importing
- discovery, Importing Resources from the Discovery Queue
- inventory
- importing, Managing the Resource Inventory
- overview, About the Inventory: Resources
- reports, Getting Inventory Reports
J
- JBoss ON
- access control, About Security in JBoss ON: Roles and Access Control
- and LDAP, Configuring LDAP User Authentication
- configuring, Configuring LDAP User Authentication
- authorization, How JBoss ON Roles Work with LDAP User Groups
- supported LDAP servers, How JBoss ON Uses LDAP for Authentication
L
- LDAP
- assigning groups to roles, About Security in JBoss ON: Roles and Access Control
- authorization, How JBoss ON Roles Work with LDAP User Groups
- for authentication, Configuring LDAP User Authentication
- configuring, Configuring LDAP User Authentication
- configuring SSL, Configuring LDAP User Authentication
- supported servers, How JBoss ON Uses LDAP for Authentication
- user groups and roles, Associating LDAP User Groups to Roles in JBoss ON
- LDAP group object classes, How JBoss ON Roles Work with LDAP User Groups
- member attributes, How JBoss ON Roles Work with LDAP User Groups
- search parameters, How JBoss ON Roles Work with LDAP User Groups
- verifying credentials, How JBoss ON Uses LDAP for Authentication
P
- permissions, About Security in JBoss ON: Roles and Access Control
- applying to groups, Creating a New Role
- assigning to users, Changing Role Assignments for Users
- changing on roles, Editing Roles
- list of, About Security in JBoss ON: Roles and Access Control
R
- reports
- inventory, Getting Inventory Reports
- resources
- access control, About Security in JBoss ON: Roles and Access Control
- access permissions on, About Security in JBoss ON: Roles and Access Control
- and managing inventory, Managing the Resource Inventory
- and roles, About Security in JBoss ON: Roles and Access Control
- creating children, Creating Child Resources
- deleting entries, Deleting Entries
- discovery and imports, Importing Resources from the Discovery Queue
- dynamic search, Dynamic Searches for Resources and Groups
- groups, Managing Groups
- ignoring discovered resources, Ignoring Discovered Resources
- inventory reports, Getting Inventory Reports
- managed, Managed Resources: Platforms, Servers, and Services
- manual discovery, Running Discovery Scans Manually
- running discovery, Importing Resources from the Discovery Queue
- search context, Property Searches
- uninventory, Removing Resources from the Inventory
- roles, About Security in JBoss ON: Roles and Access Control
- adding or removing users, Changing Role Assignments for Users
- and groups, About Security in JBoss ON: Roles and Access Control
- and LDAP user groups, Associating LDAP User Groups to Roles in JBoss ON
- LDAP group object classes, How JBoss ON Roles Work with LDAP User Groups
- member attributes, How JBoss ON Roles Work with LDAP User Groups
- searching for members, How JBoss ON Roles Work with LDAP User Groups
- and users, About Security in JBoss ON: Roles and Access Control
- assigning groups, Creating a New Role
- assigning users from LDAP groups, About Security in JBoss ON: Roles and Access Control
- changing member groups, Editing Roles
- changing permissions, Editing Roles
- creating, Creating a New Role
- default, About Security in JBoss ON: Roles and Access Control
- setting permissions, Creating a New Role
- types of members, About Security in JBoss ON: Roles and Access Control
S
- search
- groups context, Property Searches
- resource context, Property Searches
- string operators, Property Searches
- using quotation marks, Basic String Searches
- secure connections
- using for LDAP authentication, Configuring LDAP User Authentication
- security
- users, Creating User Accounts
- self-registering
- server
- access control, About Security in JBoss ON: Roles and Access Control
- global rights, About Security in JBoss ON: Roles and Access Control
- resource-level rights, About Security in JBoss ON: Roles and Access Control
- and LDAP groups for roles, Associating LDAP User Groups to Roles in JBoss ON
- building LDAP search, How JBoss ON Roles Work with LDAP User Groups
- LDAP group object classes, How JBoss ON Roles Work with LDAP User Groups
- member attributes, How JBoss ON Roles Work with LDAP User Groups
- LDAP authentication, Configuring LDAP User Authentication
- configuring, Configuring LDAP User Authentication
- SSL
- using for LDAP authentication, Configuring LDAP User Authentication
U
- UI
- A Tour of the UI, Using the JBoss ON Web Interface
- access control, About Security in JBoss ON: Roles and Access Control
- dashboard, Dashboard
- deleting entries, Deleting Entries
- details page, Entry Details Pages
- inventory, Inventory Browsers and Summaries
- left menu, The Left Menu
- logging in, Logging into the JBoss ON Web UI
- setting favorites, Setting Favorites
- users
- and roles, About Security in JBoss ON: Roles and Access Control
- assigning LDAP user groups to roles, About Security in JBoss ON: Roles and Access Control
- authentication, Configuring LDAP User Authentication
- changing access controls, Changing Role Assignments for Users
- changing roles, Changing Role Assignments for Users
- configuring LDAP authentication, Configuring LDAP User Authentication
- creating new, Creating a New User
- disabling accounts, Disabling User Accounts
- editing details, Editing User Entries
- security, Creating User Accounts
- using LDAP to self-register, How JBoss ON Uses LDAP for Authentication

