-
Language:
English
-
Language:
English
Red Hat Training
A Red Hat training course is available for JBoss Enterprise Application Platform Common Criteria Certification
Common Criteria Configuration Guide
for use with JBoss Enterprise Application Platform 6 Common Criteria Certification
Nidhi Chaudhary
Lucas Costi
Russell Dickenson
Sande Gilda
Vikram Goyal
Eamon Logue
Darrin Mison
Scott Mumford
David Ryan
Nidhi Srinivas
Misty Stanley-Jones
Keerat Verma
Tom Wells
Abstract
Chapter 1. Introduction
1.1. Purpose of this Document
1.2. JBoss EAP-specific conventions
/home directory, EAP_HOME refers to the home/USER/jboss-eap-[version]/ directory.
1.3. What is a Common Criteria Compliant System?
1.4. Certified Documentation
- PDF documentation bundle
- online
Warning
Chapter 2. Requirements for the Evaluated Configuration
2.1. Software Requirements
2.1.1. Java Virtual Machine
Table 2.1. Java Virtual Machine Version
| JVM | Version(s) |
|---|---|
| OpenJDK | 1.6.x |
| OpenJDK | 1.7.x |
| Oracle JDK | 1.6.x |
| Oracle JDK | 1.7.x |
| IBM JDK | 1.6.x |
| IBM JDK | 1.7.x |
2.1.2. Operating System
- Red Hat Enterprise Linux 5
- Red Hat Enterprise Linux 6
- Solaris 10
- Solaris 11
- Microsoft Windows Server 2008
- Microsoft Windows Server 2008 R2
- Microsoft Windows Server 2012
2.1.3. Database JDBC Drivers
Important
Table 2.2. Allowed Database and JDBC Driver Versions
| Database | JDBC Driver |
|---|---|
| IBM DB2 v9.7 |
IBM DB2 JDBC Universal Driver Architecture version 4.14.122
Driver download: http://www-947.ibm.com/support/entry/portal/Overview/Software/Information_Management/IBM_Data_Server_Client_Packages
File name:
db2jcc4.jar
SHA-256: d435d21446382019f30afb90c474d1de4152814cf1995606b52a7a5fbf4af07e
|
| IBM DB2 v10.1 |
IBM DB2 JDBC Universal Driver Architecture version 4.13.127
Driver download: http://www-947.ibm.com/support/entry/portal/Overview/Software/Information_Management/IBM_Data_Server_Client_Packages
File name:
db2jcc4.jar
SHA-256: 16858ed1b11c30a9cf14424bad173bad0b16bf61ca89614ac86f9c3d4407450e
|
| Oracle 11g R1 (v11.1.0.7.0) |
Oracle 11g R1 version 11.1.0.7
File name:
ojdbc6.jar
SHA-256: 2468c758f9b1af81201bb5b9665a6216cdbb7fb95e63b9015495d9d0edb47add
|
| Oracle 11g R1 RAC v(11.1.0.7.0) |
Oracle 11g RAC version 11.1.0.7
File name:
ojdbc6.jar
SHA-256: 2468c758f9b1af81201bb5b9665a6216cdbb7fb95e63b9015495d9d0edb47add
|
| Oracle 11g R2 |
Oracle JDBC Driver version 11.2.0.3.0
File name:
ojdbc6.jar
SHA-256: b7a8656754c891f2d9605afc6d2f4d98a5a8d6fbafe0065b24590061794b1460
|
| Oracle 11g R2 RAC |
Oracle JDBC Driver version 11.2.0.3.0
File name:
ojdbc6.jar
SHA-256: b7a8656754c891f2d9605afc6d2f4d98a5a8d6fbafe0065b24590061794b1460
|
| Oracle 12c |
|
| MySQL v5.5 |
MySQL Connector/J 5.1.23
Driver download: http://downloads.mysql.com/archives/c-j/.
File name:
mysql-connector-java-5.1.23-bin.jar
SHA-256: 9302461695b75d0d99064ab1fa237b89532deb5e39e10b0a6dd1e70b0c33bb4b
|
| Microsoft SQL Server 2008 R2 SP2 |
Microsoft SQL Server JDBC Driver 4.0.2206.100
Driver download: http://www.microsoft.com/en-au/download/details.aspx?id=11774.
File name:
sqljdbc4.jar
SHA-256: 6b423a4e8f11dc5357d1cfa38ee2a42bae87a83126fe3363b4464e5120d33f8c
|
| Microsoft SQL Server 2012 |
Microsoft SQL Server JDBC Driver 4.0.2206.100
Driver download: http://www.microsoft.com/en-au/download/details.aspx?id=11774.
File name:
sqljdbc4.jar
SHA-256: 6b423a4e8f11dc5357d1cfa38ee2a42bae87a83126fe3363b4464e5120d33f8c
|
| PostgreSQL v9.2 |
JDBC4 Postgresql Driver, version 9.2-1002
Driver download: http://jdbc.postgresql.org/download/postgresql-9.2-1002.jdbc4.jar.
File name:
postgresql-9.2-1002.jdbc4.jar
SHA-256: cd1824fa8c059e6376c92020f1e7fe6c6f34772e9f91711327e414f1b979fbe1
|
| Enterprise DB Postgres Plus Advanced Server 9.2 |
Postgres Plus Advanced Server Driver 9.2 (9.2.1.3)
Driver download: http://www.enterprisedb.com/downloads/postgres-postgresql-downloads.
File name:
edb-jdbc14.jar
SHA-256: a9c7b4519e13524c930172e8a1da4d70f585e8a96275fe002d97b38aa3619649
|
| Sybase ASE 15.7 |
Sybase jConnect JDBC driver v7.07 (Build 26792/EBF20686)
File name:
jconn4.jar
SHA-256: 1349ded4fd4a7ba6fc39b2aa353924c82d4b6812587737350af44ed949d97aee
|
Note
sha256sum command can be used on most Linux and Unix operating systems. Mac OS X includes the equivalent command shasum -a 256.
2.2. Physical Requirements
2.3. Personnel Requirements
2.4. Connectivity Requirements
2.4.1. Cluster Connectivity Requirements
- network protocol is TCP
- destination port is 8080 or 8443
Note
Chapter 3. Downloading and Verifying the Packages
Important
3.1. About the Red Hat Customer Portal
- Manage and maintain Red Hat entitlements and support contracts;
- Download officially-supported software;
- Access product documentation and the Red Hat Knowledgebase;
- Contact Global Support Services; and
- File bugs against Red Hat products.
3.2. Verify the Authenticity of the Download Site
Procedure 3.1. Checking Site Security with Firefox
- In the address bar, click the padlock icon.
- From the pop-up box, click More Information.
- From the Page Info window, click Security.
- The certificate displays details such as who owns the site, who issued the certificate, when it was issued, when it expires and fingerprint verification strings.
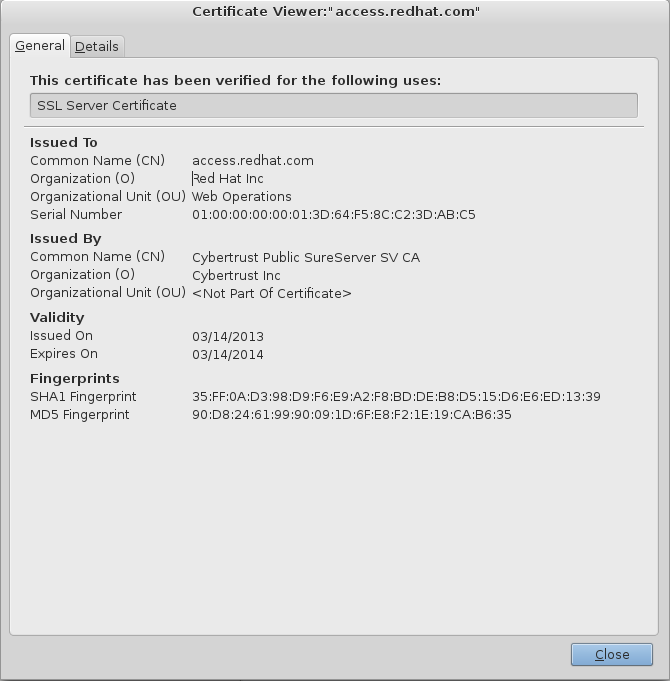
Figure 3.1. Example of the Red Hat Network SSL Certificate
3.3. Verify the Downloaded Files
sha256 command must be replaced with shasum -a 256. On Microsoft Windows, a third-party SHA256 hash sum utility is required as there is no native utility.
Procedure 3.2. Using the sha256sum tool on Linux or Unix
- Open a terminal, and navigate to the directory where the file was downloaded.
- Execute the
sha256sumcommand (or equivalent) on the file. For example:$
sha256sum jboss-eap-6.2.2.zip9414619e186708b34381ddbef1901a51335b5b45464838effb153b610b27918f jboss-eap-6.2.2.zip
The value generated by the sha256sum utility must match the value displayed on the Red Hat Customer Portal for the file. If they are not the same, your download is either incomplete or corrupt, and you will need to download the file again. If the checksum will still not successfully validate after several attempted downloads, contact Red Hat Support for assistance.
3.4. Zip Installation
3.4.1. Download JBoss EAP 6 (Zip Installation)
The JBoss EAP 6 Zip file is available from https://access.redhat.com. The Zip file installation is platform-independent and is the preferred way to install JBoss EAP 6 on all supported platforms. This topic covers the steps to download the required archive.
Procedure 3.3. Download the Zip file
- Log into the Red Hat Customer Portal at https://access.redhat.com.
- Click Downloads.
- Click Red Hat JBoss Enterprise Application Platform in the Product Downloads list.
- Select 6.2 CC from the Version drop-down menu.
- Select Red Hat JBoss Enterprise Application Platform 6.2.2 Common Criteria Zip from the list of Software Downloads.
- When the download has finished, verify that the checksum of the downloaded file matches the checksum listed on the Customer Portal. See Section 3.3, “Verify the Downloaded Files”.
JBoss EAP 6 has been downloaded successfully to the target machine, and is ready for installation.
3.4.2. Install JBoss EAP 6 (Zip Installation)
This topic covers the steps to install JBoss EAP 6.2.2 using the downloaded Zip file.
Procedure 3.4. Zip File Installation
Use an appropriate application to extract the
jboss-eap-6.2.2-cc.zipbundle.- In Red Hat Enterprise Linux and Solaris environments, use the
unziputility to extract the contents of the ZIP archive. - In a Microsoft Windows environment, right-click the file and select Extract All.
After extracting the bundle, you will have thejboss-eap-6.2.2.ziparchive and several sub-directories.Move
jboss-eap-6.2.2.zipto the desired location.Movejboss-eap-6.2.2.zipto the directory where you plan to install JBoss EAP 6. The user who will start and stop the server must have read and write access to this directory.Extract
jboss-eap-6.2.2.zipto the desired location.The directory created by extracting the Zip archive is the top-level directory for the server. This is referred to asEAP_HOME.
JBoss EAP 6.2.2 has been installed successfully.
3.5. RPM Installation from ISO
Important
Prerequisites
- Register the server on the Red Hat Network.
- Subscribe to the
Red Hat Enterprise Linux Serverbase software channel appropriate to your Red Hat Enterprise Linux version. - Do not subscribe to the
JBoss Application Platform for Serversub-channel, in theJBoss Enterprise Platformgroup.
3.5.1. Download JBoss EAP 6 ISO (RPM Installation)
Procedure 3.5. Download the JBoss EAP 6.2.2 ISO
- Log into the Red Hat Customer Portal at https://access.redhat.com.
- Click Downloads.
- Click Red Hat JBoss Enterprise Application Platform in the Product Downloads list.
- Select 6.2 CC from the Version drop-down menu.
- Click the link to the ISO to begin the download.Ensure you download the correct ISO for your version of Red Hat Enterprise Linux. For Red Hat Enterprise Linux 5, the file name is
jboss-eap-6.2.2-cc-rhel-5-noarch.isoand for Red Hat Enterprise Linux 6, the file name isjboss-eap-6.2.2-cc-rhel-6-noarch.iso. - When the download has finished, verify that the checksum of the downloaded ISO matches the checksum listed on the Customer Portal. See Section 3.3, “Verify the Downloaded Files”.
3.5.2. Install JBoss EAP 6 from ISO (RPM Installation)
Procedure 3.6. Install JBoss EAP 6 from ISO on Red Hat Enterprise Linux
Important
Mount ISO Image
Mount the ISO image downloaded in Section 3.5.1, “Download JBoss EAP 6 ISO (RPM Installation)” to/mnt/jboss.[root ~]# mkdir /mnt/jboss [root ~]# mount -o loop PATH_TO_ISO_IMAGE /mnt/jboss
Create Repository
Create a file namedjbosslocal.repoin/etc/yum.repos.d/.[root ~]# cat << EOF > /etc/yum.repos.d/jbosslocal.repo [jbosslocal] name=jbosslocal baseurl=file:///mnt/jboss enabled=1 gpgcheck=0 EOF
Install JBoss EAP 6.2.2
Run the following command:[root ~]# yum groupinstall jboss-eap6
The installation is complete. The default EAP_HOME path for the RPM installation is /usr/share/jbossas.
3.6. Confirming the Version of your JBoss EAP 6 Installation
-V with the startup script
Retrieve information about the version of your JBoss EAP 6 installation by running the same script used to start the server with only the -V switch. If your installation is a standalone or managed domain, for Red Hat Enterprise Linux, HP-UX and Solaris, this script is either standalone.sh or domain.sh, and on Microsoft Windows Server it is the equivalent .bat scripts. The startup scripts are located in EAP_HOME/bin.
-V switch will not start the server, and does not require the server to be running. It displays information about the JBoss EAP version and its configured Java environment. Below is an example of using it on an installation of JBoss EAP 6 on Red Hat Enterprise Linux. Note the version number (JBoss EAP 6.2.2.GA) displayed as the last line of the output.
$ ./standalone.sh -V
=========================================================================
JBoss Bootstrap Environment
JBOSS_HOME: /home/user/jboss-eap-6.2
JAVA: /usr/lib/jvm/java-1.7.0-openjdk.x86_64/bin/java
JAVA_OPTS: -server -XX:+UseCompressedOops -Xms1303m -Xmx1303m -XX:MaxPermSize=256m -Djava.net.preferIPv4Stack=true -Djboss.modules.system.pkgs=org.jboss.byteman -Djava.awt.headless=true
=========================================================================
14:38:11,609 INFO [org.jboss.modules] (main) JBoss Modules version 1.3.0.Final-redhat-2
14:38:11,780 INFO [stdout] (main) JBoss EAP 6.2.2.GA (AS 7.3.0.Final-redhat-14)When the JBoss EAP 6 server is running, the version information is displayed at top of the home page of the Web Console, located at http://localhost:9990/console/.
When a server is started, the version is echoed to the console, and written to the server log. For standalone configurations the server log is located at EAP_HOME/standalone/log/server.log, and for managed domain servers it is EAP_HOME/domain/servers/SERVER_NAME/log/server.log:
14:56:16,256 INFO [org.jboss.as] (Controller Boot Thread) JBAS015874: JBoss EAP 6.2.2.GA (AS 7.3.0.Final-redhat-14) started in 4872ms - Started 147 of 209 services (61 services are passive or on-demand)
3.7. Updating a Common Criteria Compliant JBoss EAP 6.2.2 Installation
Warning
3.7.1. Applying Patches to a Zip Installation
Important
- Use the
patchcommand to apply patches to your zip installation. See the Installation Guide for instructions.
3.7.2. Applying Patches to a RPM Installation from ISO
Important
Remove the local repository
Remove the file namedjbosslocal.repofrom/etc/yum.repos.d/:[root ~]#
rm /etc/yum.repos.d/jbosslocal.repo- Update the installation as a normal RPM installation. See the Installation Guide.
Chapter 4. Start and Stop JBoss EAP 6
4.1. Start JBoss EAP 6
4.2. Start JBoss EAP 6 as a Standalone Server
This topic covers the steps to start JBoss EAP 6 as a Standalone Server.
Procedure 4.1. Start the Platform Service as a Standalone Server
For Red Hat Enterprise Linux.
Run the command:EAP_HOME/bin/standalone.shFor Microsoft Windows Server.
Run the command:EAP_HOME\bin\standalone.batOptional: Specify additional parameters.
To print a list of additional parameters to pass to the start-up scripts, use the-hparameter.
The JBoss EAP 6 Standalone Server instance starts.
4.3. Start JBoss EAP 6 as a Managed Domain
The domain controller must be started before any slave servers in any server groups in the domain. Use this procedure first on the domain controller, and then on each associated host controller and each other host associated with the domain.
Procedure 4.2. Start the Platform Service as a Managed Domain
For Red Hat Enterprise Linux.
Run the command:EAP_HOME/bin/domain.shFor Microsoft Windows Server.
Run the command:EAP_HOME\bin\domain.batOptional: Pass additional parameters to the start-up script.
For a list of parameters you can pass to the start-up script, use the-hparameter.
The JBoss EAP 6 Managed Domain instance starts.
4.4. Start JBoss EAP 6 with an Alternative Configuration
Prerequisites
- Before using an alternate configuration file, prepare it using the default configuration as a template. For a Managed Domain, the configuration file needs to be placed in the
EAP_HOME/domain/configuration/directory. For a Standalone Server, the configuration file should be placed in theEAP_HOME/standalone/configuration/directory.
Note
EAP_HOME/docs/examples/configs/ directory. Use these examples to enable extra features such as clustering or the Transactions XTS API.
Procedure 4.3. Start the Instance with an Alternative Configuration
Standalone server
For a Standalone Server, provide the filename of the configuration file as an option to the--server-configparameter. The configuration file must be located in theEAP_HOME/standalone/configuration/directory, and you need to specify the file path relative to that directory.Example 4.1. Using an alternate configuration file for a Standalone Server in Red Hat Enterprise Linux
[user@host bin]$
./standalone.sh --server-config=standalone-alternate.xmlThis example uses theEAP_HOME/standalone/configuration/standalone-alternate.xmlconfiguration file.Example 4.2. Using an alternate configuration file for a Standalone Server in Microsoft Windows Server
C:\EAP_HOME\bin>
standalone.bat --server-config=standalone-alternate.xmlThis example uses theEAP_HOME\standalone\configuration\standalone-alternative.xmlconfiguration file.Managed Domain
For a Managed Domain, provide the file name of the configuration file as an option to the--domain-configparameter. The file must be present in theEAP_HOME/domain/configuration/directory, and you need to specify the path relative to that directory.Example 4.3. Using an alternate configuration file for a Managed Domain in Red Hat Enterprise Linux
[user@host bin]$
./domain.sh --domain-config=domain-alternate.xmlThis example uses theEAP_HOME/domain/configuration/domain-alternate.xmlconfiguration file.Example 4.4. Using an alternate configuration file for a Managed Domain in Microsoft Windows Server
C:\EAP_HOME\bin>
domain.bat --domain-config=domain-alternate.xmlThis example uses theEAP_HOME\domain\configuration\domain-alternate.xmlconfiguration file.
JBoss Enterprise Application Platform is now running, using your alternate configuration file.
4.5. Reference of Switches and Arguments to pass at Server Runtime
standalone.xml, domain.xml and host.xml configuration files. This might include starting the server with an alternative set of socket bindings or a secondary configuration. A list of these available parameters can be accessed by passing the help switch at startup.
Example 4.5.
-h or --help switches. The results of the help switch are explained in the table below.
[localhost bin]$ standalone.sh -h[localhost bin]$ domain.sh -hTable 4.1. Table of runtime switches and arguments
| Argument or Switch | Mode | Description |
|---|---|---|
--admin-only | Standalone | Set the server's running type to ADMIN_ONLY. This will cause it to open administrative interfaces and accept management requests, but not start other runtime services or accept end user requests. |
--admin-only | Domain | Set the host controller's running type to ADMIN_ONLY causing it to open administrative interfaces and accept management requests but not start servers or, if this host controller is the master for the domain, accept incoming connections from slave host controllers. |
-b <value>, -b=<value> | Standalone, Domain | Set system property jboss.bind.address to the given value. |
-b<interface>=<value> | Standalone, Domain | Set system property jboss.bind.address.<interface> to the given value. |
--backup | Domain | Keep a copy of the persistent domain configuration even if this host is not the Domain Controller. |
-c <config>, -c=<config> | Standalone | Name of the server configuration file to use. The default is standalone.xml. |
-c <config>, -c=<config> | Domain | Name of the server configuration file to use. The default is domain.xml. |
--cached-dc | Domain | If the host is not the Domain Controller and cannot contact the Domain Controller at boot, boot using a locally cached copy of the domain configuration. |
--debug [<port>] | Standalone | Activate debug mode with an optional argument to specify the port. Only works if the launch script supports it. |
-D<name>[=<value>] | Standalone, Domain | Set a system property. |
--domain-config=<config> | Domain | Name of the server configuration file to use. The default is domain.xml. |
-h, --help | Standalone, Domain | Display the help message and exit. |
--host-config=<config> | Domain | Name of the host configuration file to use. The default is host.xml. |
--interprocess-hc-address=<address> | Domain | Address on which the host controller should listen for communication from the process controller. |
--interprocess-hc-port=<port> | Domain | Port on which the host controller should listen for communication from the process controller. |
--master-address=<address> | Domain | Set system property jboss.domain.master.address to the given value. In a default slave Host Controller config, this is used to configure the address of the master Host Controller. |
--master-port=<port> | Domain | Set system property jboss.domain.master.port to the given value. In a default slave Host Controller config, this is used to configure the port used for native management communication by the master Host Controller. |
--read-only-server-config=<config> | Standalone | Name of the server configuration file to use. This differs from --server-config and -c in that the original file is never overwritten. |
--read-only-domain-config=<config> | Domain | Name of the domain configuration file to use. This differs from --domain-config and -c in that the initial file is never overwritten. |
--read-only-host-config=<config> | Domain | Name of the host configuration file to use. This differs from --host-config in that the initial file is never overwritten. |
-P <url>, -P=<url>, --properties=<url> | Standalone, Domain | Load system properties from the given URL. |
--pc-address=<address> | Domain | Address on which the process controller listens for communication from processes it controls. |
--pc-port=<port> | Domain | Port on which the process controller listens for communication from processes it controls. |
-S<name>[=<value>] | Standalone | Set a security property. |
--server-config=<config> | Standalone | Name of the server configuration file to use. The default is standalone.xml. |
-u <value>, -u=<value> | Standalone, Domain | Set system property jboss.default.multicast.address to the given value. |
-v, -V, --version | Standalone, Domain | Display the application server version and exit. |
Chapter 5. Configuration Requirements
5.1. WS-Transaction Support
5.2. Virtual File System (VFS) Configuration
Procedure 5.1. Configure VFS for Common Criteria Requirements
- For a zip installation, modify
EAP_HOME/modules/system/layers/base/.overlays/layer-base-jboss-eap-6.2.2.CP/org/jboss/as/server/main/module.xml:Or, for a RPM from ISO installation, modify/usr/share/jbossas/modules/system/layers/base/org/jboss/as/server/main/module.xml:Replace the line:<module name="org.jboss.vfs"/>
with:<module name="org.jboss.vfs" services="import"/>
- For a zip installation, modify
EAP_HOME/modules/system/layers/base/org/jboss/as/standalone/main/module.xml:Or, for a RPM from ISO installation, modify/usr/share/jbossas/modules/system/layers/base/org/jboss/as/standalone/main/module.xml:Add the VFS configuration within the<dependencies>element:<dependencies> ... <module name="org.jboss.vfs" services="import"/> </dependencies>
5.3. Network Configuration
5.3.1. Network Interfaces
Network Interfaces
- public
- For communication to and from external, potentially untrusted parties.
- cluster
- For communication between cluster nodes. Cannot be accessed by untrusted parties. This must be enforced as part of network/firewall configuration.
- internal
- For communication between trusted servers or users (such as administrators) via the internal network. Cannot be accessible to untrusted parties or general users of the system.
5.3.2. Network Interface Configuration
Procedure 5.2. Define and Configure Network Interfaces
Remove
unsecureNetwork Interface[standalone@localhost:9999 /]
/interface=unsecure/:removeCreate
internalandclusterNetwork Interfaces[standalone@localhost:9999 /]
/interface=cluster/:add(inet-address=expression "${jboss.bind.address.cluster:127.0.0.1}")[standalone@localhost:9999 /]/interface=internal/:add(inet-address=expression "${jboss.bind.address.internal:127.0.0.1}")Bind each socket to the specified network interface.
For each line in Table 5.1, “Network Bindings”, use the following command to bind the socket to the specified network interface. Refer to the Administration and Configuration Guide.[standalone@localhost:9999 /]
/socket-binding-group=standard-sockets/socket-binding=BINDING_NAME/:write-attribute(name=interface,value=NETWORK_INTERFACE)For example, the following command bindsmanagement-nativeto theinternalnetwork interface:[standalone@localhost:9999 /]
/socket-binding-group=standard-sockets/socket-binding=management-native/:write-attribute(name=interface,value=internal)Restart JBoss EAP
Restart JBoss EAP so that the network bindings take effect.
Table 5.1. Network Bindings
| Binding Name | Network Interface | Port Number |
|---|---|---|
| management-native | internal | 9999 |
| management-http | internal | 9990 |
| management-https | internal | 9443 |
| ajp | internal | 8009 |
| http | public | 8080 |
| https | public | 8443 |
| jacorb | internal | 3528 |
| jacorb-ssl | internal | 3529 |
| jgroups-mping | cluster | 0 - multicast: 45700 |
| jgroups-tcp | cluster | 7600 |
| jgroups-tcp-fd | cluster | 57600 |
| jgroups-udp | cluster | 55200 - multicast: 45688 |
| jgroups-udp-fd | cluster | 54200 |
| messaging | internal | 5445 |
| messaging-group | internal | 0 - multicast: 9876 |
| messaging-throughput | internal | 5455 |
| modcluster | public/internal | 0 - multicast: 23364 |
| remoting | internal | 4447 |
| txn-recovery-environment | internal | 4712 |
| txn-status-manager | internal | 4713 |
5.4. Security Configuration
5.4.1. About Authorization
Note
5.4.2. Java Security Manager Policy File
Procedure 5.3. Install Common Criteria-evaluated Security Manager Policy
Create the Common Criteria-evaluated Policy File
Copy the following text into a text editor and save it inEAP_HOME/bin/directory. The suggested file name isjbosseap62.policy.// Grant all to the jboss-modules.jar grant codeBase "file:${jboss.home.dir}/jboss-modules.jar" { permission java.security.AllPermission; }; // Standard extensions get all permissions by default grant codeBase "file:${java.home}/lib/ext/*" { permission java.security.AllPermission; };Note
The CC-evaluated policy file may need additional permissions configured, such as permissions to database drivers. These permissions are site-specific.Configure the Java Parameters
Add the following Java command line parameters to the JBoss EAP start-up configuration scripts (standalone.conf, domain.conf, standalone.conf.bat, domain.conf.bat):- -Djava.security.manager
- Enables the security manager
- -Djava.security.policy==/path/to/security.policy
- Specify the path to the security policy file.
- -Djboss.home.dir=/path/to/JBOSS_EAP_HOME
- Define the system property that is used in the policy file.
- -Djboss.modules.policy-permissions=true
- Enables deployment level security permissions.
Example 5.1. standalone.conf
JAVA_OPTS="$JAVA_OPTS -Djava.security.manager -Djava.security.policy==$JBOSS_HOME/bin/jbosseap62.policy -Djboss.home.dir=$JBOSS_HOME -Djboss.modules.policy-permissions=true"
Note
The JBOSS_HOME environment variable is not defined when domain.conf is processed. It can be used only in standalone.conf.Configure the Java Security Manager to use the policy file
See Java Security Manager in the Security Guide.
5.4.3. Enable Audit Logging
Note
Procedure 5.4. Enable Audit Logging
- Create a periodic rotating file handler named
AUDIT. The format of log file must be defined with this format to be common criteria compliant./subsystem=logging/periodic-rotating-file-handler=AUDIT/:add(suffix=.yyyy-MM-dd,formatter=%d{HH:mm:ss,SSS} %-5p [%c] (%t) %s%E%n,level=TRACE,file={"relative-to" => "jboss.server.log.dir","path" => "audit.log"}) - Create a logger category for the JBoss EAP logging subsystem.
/subsystem=logging/logger=org.jboss.security.audit/:add(level=TRACE,category=org.jboss.security.audit,handlers=["AUDIT"])
- Enable audit logging in each application by using the
jboss-web.xmldescriptor located in theWEB-INFdirectory, setting the tagdisable-audittofalse.<?xml version="1.0" encoding="UTF-8"?> <jboss-web> <security-domain>security_domain_for_the_app</security-domain> <disable-audit>false</disable-audit> </jboss-web>
5.4.4. Management Interface Audit Logging
5.4.4.1. About Management Interface Audit Logging
Note
5.4.4.2. Enable Management Interface Audit Logging from the Management CLI
/core-service=management/access=audit/logger=audit-log:write-attribute(name=enabled,value=true)
5.4.4.3. About a Management Interface Audit Logging Formatter
Table 5.2. JSON Formatter Fields
| Attribute | Description |
|---|---|
| include-date | Boolean value which defines whether or not the timestamp is included in the formatted log records. |
| date-separator | A string containing characters to separate the date and the rest of the formatted log message. Will be ignored if include-date=false. |
| date-format | The date format to use for the timestamp as understood by java.text.SimpleDateFormat. Ignored if include-date=false. |
| compact | If true it will format the JSON on one line. There may still be values containing new lines, so if having the whole record on one line is important, set escape-new-line or escape-control-characters to true. |
| escape-control-characters | If true it will escape all control characters (ASCII entries with a decimal value < 32) with the ASCII code in octal; for example, a new line becomes '#012'. If this is true, it will override escape-new-line=false. |
| escape-new-line | If true it will escape all new lines with the ASCII code in octal; for example #012. |
5.4.4.4. About a Management Interface Audit Logging File Handler
Table 5.3. File Handler Audit Log Fields
| Attribute | Description | Read Only |
|---|---|---|
| formatter | The name of a JSON formatter to use to format the log records. | False |
| path | The path of the audit log file. | False |
| relative-to | The name of another previously named path, or of one of the standard paths provided by the system. If relative-to is provided, the value of the path attribute is treated as relative to the path specified by this attribute. | False |
| failure-count | The number of logging failures since the handler was initialized. | True |
| max-failure-count | The maximum number of logging failures before disabling this handler. | False |
| disabled-due-to-failure | true if this handler was disabled due to logging failures. | True |
5.4.4.5. About a Management Interface Audit Logging Syslog Handler
http://www.ietf.org/rfc/rfc3164.txthttp://www.ietf.org/rfc/rfc5424.txthttp://www.ietf.org/rfc/rfc6587.txt
Table 5.4. Syslog Handler Fields
| Field | Description | Read-only |
|---|---|---|
formatter | The name of the formatter to use to format the log records. | False |
failure-count | The number of logging failures since the handler was initialized | True |
max-failure-count | The maximum number of logging failures before disabling this handler. | False |
disabled-due-to-failure | True if this handler was disabled due to logging failures. | True |
syslog-format | Syslog format: RFC-5424 or RFC-3164. | False |
| max-length | The maximum length of a log message (in bytes), including the header. If undefined, it will default to 1024 bytes if the syslog-format is RFC3164, or 2048 bytes if the syslog-format is RFC5424. | False. |
truncate | Whether or not a message, including the header, should truncate the message if the length in bytes is greater than the maximum length. If set to false messages will be split and sent with the same header values. | False |
5.4.4.6. Enable Management Interface Audit Logging to a Syslog Server
Note
/host=HOST_NAME to the /core-service commands if the change is to be applied to a managed domain.
Procedure 5.5. Enable Logging to a Syslog Server
Create a syslog handler named
msyslog[standalone@localhost:9999 /]batch [standalone@localhost:9999 /]/core-service=management/access=audit/syslog-handler=mysyslog:add(formatter=json-formatter) [standalone@localhost:9999 /]/core-service=management/access=audit/syslog-handler=mysyslog/protocol=udp:add(host=localhost,port=514) [standalone@localhost:9999 /]run-batch
Add a reference to the syslog handler.
[standalone@localhost:9999 /]/core-service=management/access=audit/logger=audit-log/handler=mysyslog:add
Management interface audit log entries are logged on the syslog server.
5.4.4.7. Management Interface Audit Logging Options
Configuration Options
- log-boot
- If set to
true, management operations when booting the server are included in the audit log,falseotherwise. Default:false. - log-read-only
- If set to
true, all operations will be audit logged. If set tofalseonly operations that change the model will be logged. Default:false.
5.4.4.8. Management Interface Audit Log Fields
Table 5.5. Management Interface Audit Log Fields
| Field Name | Description |
|---|---|
| type | This can have the values core, meaning it is a management operation, or jmx meaning it comes from the JMX subsystem (see the JMX subsystem for configuration of the JMX subsystem's audit logging). |
| r/o | true if the operation does not change the management model, false otherwise. |
| booting | true if the operation was executed during the bootup process, false if it was executed once the server is up and running. |
| version | Version number of the JBoss EAP instance. |
| user | Username of the authenticated user. If the operation has been logged via the CLI on the same computer as the running server, the special $local user is used. |
| domainUUID | An identifier to link together all operations as they are propagated from the doman controller to its servers, slave host controllers, and slave host controller servers. |
| access | This can have one of the following values: NATIVE, HTTP, JMX. NATIVE - The operation came in through the native management interface, for example the CLI. HTTP - The operation came in through the domain HTTP interface, for example the admin console. JMX - The operation came in through the JMX subsystem. See JMX for how to configure audit logging for JMX. |
| remote-address | The address of the client executing this operation. |
| success | true if the operation succeeded, false if it was rolled back. |
| ops | The operations being executed. This is a list of the operations serialized to JSON. At boot this will be all the operations resulting from parsing the XML. Once booted the list will typically contain a single entry. |
5.4.5. PicketBox
- File based authentication using UsersRolesLoginModule
- File based authentication for EJB Remoting Framework using RemotingLoginModule
- Certificate based authentication using BaseCertLoginModule
- LDAP based authentication using LdapLoginModule
- Advanced LDAP based authentication using LdapExtLoginModule
- Database based authentication using DatabaseServerLoginModule
5.4.6. EJB Authorization Policy
code=Delegating
code=JACC
JACCAuthorizationModule or DelegatingAuthorizationModule, refer to the Authentication chapter in the Security Guide.
5.5. Database Configuration
Note
Procedure 5.6. Configure Database
Remove ExampleDS and h2 database driver
Using the CLI, execute the following commands to remove the example DS, and h2 database driver:[standalone@localhost:9999 /]
/subsystem=datasources/data-source=ExampleDS/:remove[standalone@localhost:9999 /]/subsystem=datasources/jdbc-driver=h2/:removeAdd JDBC Grant Statement
Add the followinggrantstatement to the Java Security Manager policy file for the JDBC driver you are using. The policy file is located atEAP_HOME/bin/eap62.policy. Substitute the directory name of the JDBC driver where [cc.jdbc.driver] is specified in the code sample.Important
Each JDBC driver can use different permissions. Check the JDBC driver documentation and replacejava.security.AllPermission;with a secure permission scheme supported by the driver.// granting permissions to JDBC driver grant codeBase "file:${jboss.home.dir}/standalone/deployments/[cc.jdbc.driver]" { permission java.security.AllPermission; };
5.6. Guidance on Configuring Java Security Permissions
Warning
- file permissions, except to files that are dedicated to the application
- network permissions
- permissions to load native code.
Important
java.security.AllPermission (or equivalent for your JDBC driver) to any of the user applications interacting with the certified system.
TestDeployment.ear in the deploy directory of the certified system, then an example entry would be the following:
grant codeBase "file:${jboss.server.home.dir}/deploy/TestDeployment.ear/-" {
permission java.util.PropertyPermission "*", "read";
permission javax.security.auth.AuthPermission "createLoginContext.a_login";
permission javax.security.auth.AuthPermission "getLoginConfiguration";
};TestDeployment.ear to read Java properties as well as the ability to create JAAS login context and obtain JAAS login configuration.
javax.management.MBeanPermission as specified in the Java MbeanServer interface:
Chapter 6. Development Guide for the Common Criteria Certified System
6.1. Enterprise Application
- Web Applications based on Servlets and Java Server Pages (JSP)
- Enterprise Java Beans (EJB)
- JavaEE 1.6 Web Service Applications which can be based on Stateless EJBs or Plain Old Java Objects (POJOs) deployed as Java Servlets.
6.2. General Restrictions
- Application Programming Interfaces (APIs) that are not documented in the applicable product documentation must not be used.
- The programming restrictions mandated by the Enterprise JavaBeans Specification v2.1 must be strictly followed. For more information, refer to JSR-000153 Enterprise JavaBeans 2.1 specification. (Section 25.2, pages 562-564).
The restrictions are:
- An enterprise bean must not use read/write static fields. Using read-only static fields is allowed. Therefore, it is recommended that all static fields in the enterprise bean class be declared as final.
- An enterprise bean must not use thread synchronization primitives to synchronize execution of multiple instances.
- An enterprise bean must not use the AWT functionality to attempt to output information to a display or to input information from a keyboard.
- An enterprise bean must not use the
java.iopackage to attempt to access files and directories in the file system. - An enterprise bean must not attempt to listen on a socket, accept connections on a socket, or use a socket for multicast.
- The enterprise bean must not attempt to query a class to obtain information about the declared members that are not otherwise accessible to the enterprise bean because of the security rules of the Java language. The enterprise bean must not attempt to use the Reflection API to access information that the security rules of the Java programming language make unavailable.
- The enterprise bean must not attempt to
- create a class loader
- obtain the current class loader
- set the context class loader
- set security manager
- create a new security manager
- stop the JVM
- or change the input, output, and error streams
- The enterprise bean must not attempt to set the socket factory used by ServerSocket, Socket, or the stream handler factory used by URL.
- The enterprise bean must not attempt to manage threads. The enterprise bean must not attempt to start, stop, suspend, or resume a thread, or to change a thread's priority or name. The enterprise bean must not attempt to manage thread groups.
- The enterprise bean must not attempt to obtain the security policy information for a particular code source.
- The enterprise bean must not attempt to load a native library.
- The enterprise bean must not attempt to gain access to packages and classes that the usual rules of the Java programming language make unavailable to the enterprise bean.
- The enterprise bean must not attempt to define a class in a package.
- The enterprise bean must not attempt to access or modify the security configuration objects (Policy, Security, Provider, Signer, and Identity).
- The enterprise bean must not attempt to use the subclass and object substitution features of the Java Serialization Protocol.
- The enterprise bean must not attempt to pass this as an argument or method result. The enterprise bean must pass the result of
SessionContext.getEJBObject,SessionContext.getEJBLocalObject,EntityContext.getEJBObject, orEntityContext.getEJBLocalObjectinstead. - The enterprise bean must not use Simple and Protected GSSAPI Negotiation Mechanism (SPNEGO).
- The enterprise bean must not use annotations from PicketBox. The following annotations that modify the behavior of the JAAS module must not be used:
@AuthenticationMechanism@SecurityMapping@Authentication@Authorization@SecurityConfig@SecurityAudit
6.3. Developer Advice for User Credentials in Remote Method Invocation
setPrincipal and setCredential methods.
Example 6.1. Setting Principal and Credential
MethodInvocation mi = new MethodInvocation();
mi.setPrincipal(new SimplePrincipal("myusername"));
mi.setCredential("mypassword");Example 6.2. Retrieving Principal and Credential
Principal p = mi.getPrincipal(); Object cred = mi.getCredential(); // Now do authentication (and then authorization)
Chapter 7. Overview of the Security Functions
7.1. Access Control
- HTTP
- URLs and paths provided with URLs, as well as Plain Old Java Objects (POJOs) deployed as Servlets and Session Beans, can be protected from access by subjects.
- EJB
- EJBs and associated method names can be protected from invocation by subjects.
- HornetQ
- Message queue destinations and topic destinations can be protected from access by subjects.
7.2. Role-Based Access Control for Management Interfaces
- Model operations, whose the main function is to read/write from the model, although there will often be associated runtime services started/stopped as a consequence.
- RPC operations, which invokes some runtime that affects runtime state only. This may either read runtime state or change it. The model is not affected.
- A resource.
- An attribute residing in a resource.
Role-based access control pre-configured management roles
- Monitor
- The monitor role has the fewest permissions and restricts the user to viewing the configuration and the current state. The monitor role does not have permission to view sensitive data.
- Configurator
- The configurator role has the same permissions as the monitor role, and can change the configuration. For example, the configurator can deploy an application. The configurator role does not have permission to view sensitive data.
- Operator
- The operator role has monitor permissions and can also change the runtime state, but not the persistent configuration. For example, the operator can start or stop servers. The operator role does not have permission to view sensitive data.
- Administrator
- The administrator role has the combined permissions of the operator and the configurator. This role has also permission to access sensitive data, including passwords. The administrator role is the superuser of the Application Server and can modify administrative users and roles.
- Deployer
- The deployer role has the combined permissions of the operator and the configurator, but with those permissions constrained to operating on deployments.
- Auditor
- The auditor role can view and modify the configuration settings for the security auditing system. The auditor role includes the monitor role, allowing the auditor to view but not change the rest of the security configuration.
domain.xml or standalone.xml depending on the startup mode). The administrative interfaces are an in-memory image of the data stored in the configuration file. Once the in-memory image is modified, the modified configuration file is stored.
7.3. Audit
7.4. Clustering
- Replication of the state of a node includes the replication of HTTP sessions, EJB 3.0 session beans, EJB 3.0 entity beans, as well as Hibernate persistence objects (distributed state replication service using Infinispan).
- Replication of the state of a node covering the replication of HTTP sessions, and EJB 2.x session beans.
- Replication of HornetQ queues. Messages sent to a distributed queue or topic on one node are consumable on other nodes.
7.5. Identification and Authentication
- HTTP and webservices
- HTTP-basic authentication, HTTP-digest authentication, form-based authentication, client certificate-based authentication.
- EJB
- Username and password-based authentication, client certificate-based authentication.
- HornetQ
- Username and password-based authentication.
- File-based authentication using
UsersRolesLoginModule. - File-based authentication for EJB Remoting Framework using
RemotingLoginModule. - Certificate-based authentication using
BaseCertLoginModule. - LDAP-based authentication using
LdapLoginModule. - Advanced LDAP-based authentication using
LdapExtLoginModule. - Database based-authentication using
DatabaseServerLoginModule.
PrincipalsSet:
- A
java.security.Principalthat corresponds to the client identity as known in the deployment security environment. - A
java.security.acl.GroupnamedRolesthat contains the role names from the application domain to which the user has been assigned.org.jboss.security.SimplePrincipalobjects, or custom objects registered asprincipalClass, are used to represent the role names.SimplePrincipalis a simple string-based implementation ofPrincipal. These roles are used to validate the roles assigned to methods inejb-jar.xmland theEJBContext.isCallerInRole(String)method implementation.
7.6. Transaction Rollback
- Atomicity
- A transaction must be atomic. This means that either all the work done in the transaction must be performed, or none of it must be performed. Doing only part of a transaction is not allowed.
- Consistency
- When a transaction is completed, the system must be in a stable and consistent condition.
- Isolation
- Different transactions must be isolated from each other. This means that the partial work done in one transaction is not visible to other transactions until the transaction is committed, and that each process in a multi-user system can be programmed as if it was the only process accessing the system.
- Durability
- The changes made during a transaction are made persistent when it is committed. When a transaction is committed, its changes will not be lost, even if the server crashes afterward.
- transactions are short lived
- resources (such as databases) are locked for the duration of the transaction
- participants have a high degree of trust with each other.
Appendix A. Network Ports Used By JBoss EAP 6
- Whether your server groups use one of the default socket binding groups, or a custom group.
- The requirements of your individual deployments.
Note
8080, and your server uses a port offset of 100, its HTTP port is 8180.
The default socket binding groups
full-ha-socketsfull-socketsha-socketsstandard-sockets
Table A.1. Reference of the default socket bindings
| Name | Port | Multicast Port | Description | full-ha-sockets | full-sockets | ha-socket | standard-socket |
|---|---|---|---|---|---|---|---|
ajp | 8009 | Apache JServ Protocol. Used for HTTP clustering and load balancing. | Yes | Yes | Yes | Yes | |
http | 8080 | The default port for deployed web applications. | Yes | Yes | Yes | Yes | |
https | 8443 | SSL-encrypted connection between deployed web applications and clients. | Yes | Yes | Yes | Yes | |
jacorb | 3528 | CORBA services for JTS transactions and other ORB-dependent services. | Yes | Yes | No | No | |
jacorb-ssl | 3529 | SSL-encrypted CORBA services. | Yes | Yes | No | No | |
jgroups-diagnostics | 7500 | Multicast. Used for peer discovery in HA clusters. Not configurable using the Management Interfaces. | Yes | No | Yes | No | |
jgroups-mping | 45700 | Multicast. Used to discover initial membership in a HA cluster. | Yes | No | Yes | No | |
jgroups-tcp | 7600 | Unicast peer discovery in HA clusters using TCP. | Yes | No | Yes | No | |
jgroups-tcp-fd | 57600 | Used for HA failure detection over TCP. | Yes | No | Yes | No | |
jgroups-udp | 55200 | 45688 | Unicast peer discovery in HA clusters using UDP. | Yes | No | Yes | No |
jgroups-udp-fd | 54200 | Used for HA failure detection over UDP. | Yes | No | Yes | No | |
messaging | 5445 | JMS service. | Yes | Yes | No | No | |
messaging-group | Referenced by HornetQ JMS broadcast and discovery groups. | Yes | Yes | No | No | ||
messaging-throughput | 5455 | Used by JMS Remoting. | Yes | Yes | No | No | |
mod_cluster | 23364 | Multicast port for communication between JBoss EAP 6 and the HTTP load balancer. | Yes | No | Yes | No | |
osgi-http | 8090 | Used by internal components which use the OSGi subsystem. Not configurable using the Management Interfaces. | Yes | Yes | Yes | Yes | |
remoting | 4447 | Used for remote EJB invocation. | Yes | Yes | Yes | Yes | |
txn-recovery-environment | 4712 | The JTA transaction recovery manager. | Yes | Yes | Yes | Yes | |
txn-status-manager | 4713 | The JTA / JTS transaction manager. | Yes | Yes | Yes | Yes |
In addition to the socket binding groups, each host controller opens two more ports for management purposes:
9990- The Web Management Console port9999- The port used by the Management Console and Management API
Appendix B. Modules
- Static Modules
- Static Modules are predefined in the
EAP_HOME/modules/directory of the application server. Each sub-directory represents one module, and contains a configuration file (module.xml) and any required JAR files. The name of the module is defined in themodule.xmlfile. All the application server provided APIs are provided as static modules, including the Java EE APIs as well as other APIs such as JBoss Logging.Example B.1. Example module.xml file
<?xml version="1.0" encoding="UTF-8"?> <module xmlns="urn:jboss:module:1.0" name="com.mysql"> <resources> <resource-root path="mysql-connector-java-5.1.15.jar"/> </resources> <dependencies> <module name="javax.api"/> <module name="javax.transaction.api"/> </dependencies> </module>The module name,com.mysql, should match the directory structure for the module.Creating custom static modules can be useful if many applications are deployed on the same server that use the same third party libraries. Instead of bundling those libraries with each application, a module containing these libraries can be created and installed by the JBoss administrator. The applications can then declare an explicit dependency on the custom static modules. - Dynamic Modules
- Dynamic Modules are created and loaded by the application server for each JAR or WAR deployment (or subdeployment in an EAR). The name of a dynamic module is derived from the name of the deployed archive. Because deployments are loaded as modules, they can configure dependencies and be used as dependencies by other deployments.
Appendix C. Revision History
| Revision History | |||
|---|---|---|---|
| Revision 6.2.2-15 | Tue June 24 2014 | Tom Wells, Russell Dickenson, Lucas Costi | |
| |||

